We may not have the course you’re looking for. If you enquire or give us a call on +971 8000311193 and speak to our training experts, we may still be able to help with your training requirements.
Training Outcomes Within Your Budget!
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

As we saw the progress of technology, we also witnessed all the threats this industry was exposed to. To combat all these threats and to have proper Cybersecurity, several measures were taken by all the countries. This is where Penetration Testing comes into play. But What is Penetration Testing?
According to Statista, the global Cybersecurity market is predicted to grow at a rate of 13% by the year 2025. Penetration Testing is a process designed to unearth vulnerabilities within computer systems, networks, and applications. It simulates the tactics of potential attackers, uncovering weak points that might otherwise remain hidden. In this blog, you are going to learn about What is Penetration Testing, its importance, the different types of Penetration Testing and more.
Table of Contents
1) What is Penetration Testing?
2) The importance of Penetration Testing
3) Types of Penetration Testing
4) The Penetration Testing process
5) Conclusion
What is Penetration Testing?
Penetration Testing, often referred to as "pen testing," is a proactive and systematic approach to evaluating the security strength of digital systems and infrastructures. It involves deploying controlled, Ethical Hacking techniques to simulate real-world cyberattacks. By meticulously scrutinising networks, applications, and even physical security, Penetration Testing seeks to unveil hidden weak points, misconfigurations, or potential gaps in defence mechanisms.
This dynamic process encompasses an array of methodologies tailored to different targets. These targets can be network environments, web applications, wireless networks, and even the human factor through social engineering. By simulating actual breach attempts, organisations gain insights into how their systems would fare against determined adversaries. It also serves as a vital test for an organisation's security posture. This testing helps organisations to enable proactive measures to increase defences and safeguard sensitive information.
The importance of Penetration Testing
Penetration Testing is extremely important where cyber threats are more than ever. Here are several key reasons why Penetration Testing holds such significance:
1) Vulnerability detection: Penetration Testing systematically identifies vulnerabilities that might be overlooked by automated security tools. This helps in ensuring a comprehensive assessment of potential weak points.
2) Proactive Risk Management: By uncovering vulnerabilities before they are exploited, organisations can take proactive measures to address these issues, thereby minimising the potential impact of cyberattacks.
3) Real-world simulation: Penetration Testing mimics the tactics of real attackers, providing an authentic assessment of how systems would fare in the face of genuine cyber threats.
4) Enhanced defence strategies: Insights gained from Penetration Testing empower organisations to fortify their security infrastructure, patching vulnerabilities and shoring up defences to prevent unauthorised access.
5) Regulatory compliance: Many companies are subject to stringent data protection regulations. Penetration Testing assists in meeting compliance requirements and demonstrating due diligence in safeguarding sensitive data.
6) Protection of reputation: A successful cyberattack can tarnish an organisation's reputation and erode customer trust. Penetration Testing helps prevent breaches and assures stakeholders that security is a top priority.
7) Cost savings: Detecting and mitigating vulnerabilities early can save organisations significant costs associated with data breaches, legal actions, and remediation efforts.
8) Third-party validation: Penetration Testing provides an objective assessment of security measures, enhancing credibility for clients, partners, and stakeholders.
9) Continuous improvement: Regular Penetration Testing encourages a culture of ongoing security improvement, fostering vigilance and adaptability in the face of evolving threats.
10) Risk prioritisation: Penetration Testing reports provide actionable insights. It also helps organisations prioritise and allocate resources effectively to address the most critical vulnerabilities.
Increase your knowledge of Cybersecurity and Ethical Hacking with our Ethical Hacking Training .
Types of Penetration Testing
In this section, you are going to learn about the various types of Penetration Testing. These types are:
Network Penetration Testing
It is a critical part of Penetration Testing. It is designed to assess the security resilience of an organisation's network infrastructure. It looks into the intricate fabric of network components, from routers and firewalls to servers and workstations, with the goal of identifying vulnerabilities that malicious actors could exploit. Here's a closer look at the significance and process of Network Penetration Testing:
1) Significance: Networks serve as the backbone of modern enterprises. They carry sensitive information and facilitate communication. Yet, their complexity leaves room for vulnerabilities that can be exploited. Network Penetration Testing plays a pivotal role in the following:
a) Vulnerability identification: Uncovering vulnerabilities such as misconfigurations, weak passwords, and outdated software that can compromise network integrity.
b) Risk mitigation: By exposing potential points of entry, organisations can proactively mitigate risks, reducing the chances of successful cyberattacks.
c) Defence strengthening: Insights gained from network penetration testing guide the enhancement of network security measures, ensuring robust protection against various threats.
2) Process: Network Penetration Testing typically follows a systematic approach:
a) Scoping: Defining the scope and objectives of the test, specifying the range of systems, IPs, and components to be assessed.
b) Information gathering: Collecting data about the network architecture, IP ranges, and potential entry points through Open-Source Intelligence (OSINT) techniques.
c) Vulnerability scanning: Employing tools to scan for open ports, services, and potential vulnerabilities within the network.
d) Exploitation: Attempting to exploit known vulnerabilities to gain unauthorised access, replicating the actions of potential attackers.
e) Post-exploitation: Once access is gained, testers explore the extent of control they can exert, simulating an attacker's persistence.
f) Analysis and reporting: The results are analysed, and a detailed report is generated, outlining vulnerabilities, exploitation methods, and recommendations for remediation.
Web application Penetration Testing
It is a specialised form of security assessment aimed at evaluating the security posture of web applications. This testing methodology scrutinises the digital interfaces that users interact with, identifying vulnerabilities that could potentially be exploited by malicious hackers. Here are some more points:
1) Significance: Web applications are susceptible to a range of cyber threats due to their interconnectedness, complexity, and user interaction. Web application Penetration Testing is crucial for the following:
a) Identifying vulnerabilities: Discovering vulnerabilities like SQL injection, cross-site scripting (XSS), and insecure authentication mechanisms that could lead to data breaches and unauthorised access.
b) Protecting sensitive data: Ensuring the confidentiality, integrity, and availability of sensitive user data stored or processed by web applications.
c) Maintaining user trust: By fortifying web applications against attacks, organisations maintain the trust of users who entrust them with personal information.
2) Process: Web application Penetration Testing typically follows a structured approach:
a) Information gathering: Understanding the application's architecture, technologies used, entry points, and potential vulnerabilities through reconnaissance.
b) Vulnerability scanning: Automated tools scan the application for known vulnerabilities and security misconfigurations.
c) Manual testing: Ethical hackers employ manual techniques to uncover complex vulnerabilities that automated tools might miss.
d) Exploitation: Attempting to exploit identified vulnerabilities to demonstrate their potential impact.
e) Authentication and authorisation testing: Evaluating the effectiveness of authentication and authorisation mechanisms in place.
f) Data validation and input testing: Assessing how the application handles user inputs to prevent common vulnerabilities like SQL injection and XSS.
g) Reporting: A comprehensive report is generated detailing discovered vulnerabilities, exploitation methods, and recommendations for mitigation.
Wireless network Penetration Testing
It is a specialised assessment that focuses on evaluating the security of wireless networks, which includes Wi-Fi and other wireless communication technologies. With the ubiquity of wireless connectivity, securing these networks is paramount to prevent unauthorised access, data breaches, and potential compromise of sensitive information. Here's a closer look at the significance and process of Wireless network Penetration Testing:
1) Significance: Wireless networks provide convenience but also present significant security challenges. Wireless Network Penetration Testing is vital for:
a) Securing data transmission: Ensuring the confidentiality and integrity of data transmitted over wireless networks, preventing eavesdropping and data interception.
b) Preventing unauthorised access: Identifying weak points that attackers could destroy to gain unauthorised access to the network.
c) Protecting devices: Verifying the security of devices connected to the wireless network, including laptops, smartphones, and Internet of Things (IoT) devices.
2) Process: Wireless network Penetration Testing follows a systematic approach:
a) Information gathering: Understanding the network topology, SSIDs (network names), encryption methods, and wireless devices in use.
b) Network mapping: Identifying access points, routers, and connected devices to assess the network's architecture.
c) Wireless traffic analysis: Analysing wireless traffic to identify potential vulnerabilities and gather information about devices and their interactions.
d) Vulnerability scanning: Scanning for weak encryption, misconfigured access points, and other vulnerabilities.
e) Authentication and authorisation testing: Evaluating the security of authentication and authorisation mechanisms, including password policies and encryption protocols.
f) Exploitation: Attempting to exploit identified vulnerabilities to demonstrate their potential impact.
g) Reporting: A detailed report is generated, outlining discovered vulnerabilities, potential risks, and recommendations for mitigation.
Social engineering Penetration Testing
It is a unique security assessment that targets the human element rather than technical vulnerabilities. Leveraging psychological manipulation and deception, this form of testing simulates real-world scenarios to evaluate an organisation's susceptibility to social engineering attacks. Here's an in-depth look at the significance and process of social engineering Penetration Testing:
1) Significance: Social Engineering Penetration Testing holds importance in:
a) Human vulnerability analysis: Identifying human behaviours and tendencies that could be exploited by attackers, including trust, curiosity, and a willingness to help.
b) User awareness and training: Highlighting the need for ongoing security training and awareness programs to empower individuals to recognise and resist social engineering attempts.
c) Risk mitigation: By uncovering vulnerabilities in organisational response to social engineering, organisations can take preventive measures to mitigate the risk of breaches.
2) Process: Social Engineering Penetration Testing follows a methodical approach:
a) Information gathering: Gathering publicly available information about the organisation, its employees, and its systems.
b) Pretext creation: Crafting convincing pretexts or scenarios to manipulate individuals to indulge in sensitive information or perform actions they shouldn't.
c) Engagement: Engaging with targeted individuals via methods like phishing emails, phone calls, or physical access attempts.
d) Assessment: Evaluating responses and actions of individuals to determine the success of social engineering tactics.
e) Reporting: A detailed report is generated outlining successful social engineering attempts, vulnerabilities, and recommendations for strengthening defences.
Physical Penetration Testing
It is a distinctive facet of security assessment that delves into the tangible world, assessing an organisation's physical security measures and vulnerabilities. This form of testing involves attempting to gain unauthorised access to premises, sensitive areas, or physical assets to evaluate the effectiveness of security controls. Here's a closer look at the significance and process of physical Penetration Testing:
1) Significance: Physical security is a critical component of comprehensive defence strategies. Physical Penetration Testing holds significance in:
a) Realistic security assessment: Providing insights into how well physical security measures deter, detect, and respond to unauthorised access attempts.
b) Gap identification: Identifying weaknesses such as inadequate access controls, poor employee awareness, or vulnerabilities that could lead to breaches.
c) Risk mitigation: By revealing vulnerabilities, organisations can take corrective actions to enhance physical security, preventing unauthorised entry and safeguarding assets.
2) Process: Physical Penetration Testing follows a structured approach:
a) Planning: Defining the scope, objectives, and target areas for the test, such as entry points, secure areas, and employee interactions.
b) Reconnaissance: Gathering information about the physical layout, security protocols, and potential entry points.
c) Access attempts: Engaging in activities to gain unauthorised access, which may involve tailgating, lock picking, or bypassing security controls.
d) Employee interaction: Testing employee responses to unauthorised access attempts, gauging their awareness and adherence to security protocols.
e) Documentation: Comprehensive documentation of findings, including successful breaches, vulnerabilities, and recommendations.
f) Reporting: A detailed report outlines vulnerabilities, entry points, and actionable recommendations for strengthening physical security.
Take command of cybersecurity – sign up now for our Mastering Metasploit Framework Course.
The Penetration Testing process
To fully understand Penetration Testing, you need to understand how this process works. These points will help you to understand this process:
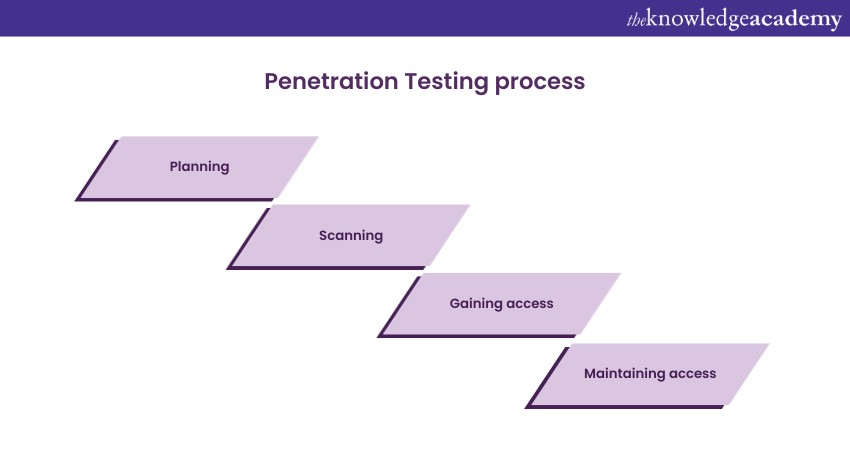
Planning
This constitutes the foundational phase of the Penetration Testing process. It sets the stage for a methodical and effective security assessment. This phase is akin to charting a course before embarking on a journey, where meticulous preparation and thorough research are key to a successful outcome.
During this crucial step, the Penetration Testing team collaborates with the client to define the scope, goals, and objectives of the assessment. Clear communication ensures that expectations are aligned, and potential risks are understood. Factors like the systems to be tested, the potential impact of the assessment, and the time frame are all carefully considered.
Scanning
It represents a pivotal phase within the Penetration Testing process, where the focus shifts from initial planning and reconnaissance to the technical assessment of the target environment. This phase involves using specialised tools to conduct an in-depth analysis of the system's network architecture, services, and potential vulnerabilities. It's akin to employing a virtual magnifying glass to scrutinise the digital landscape for weak points and entryways.
Automated scanning tools, meticulously chosen based on the target's technology stack, are employed to scan for open ports, identify active services, and detect potential misconfigurations. These tools provide a snapshot of the network's current state, forming the basis for further investigation. The scanning phase is essential for mapping out the attack surface, providing insights into the system's exposure to potential threats, and highlighting areas that require closer examination.
Gaining access
It is a pivotal stage within the Penetration Testing process where ethical hackers shift from passive assessment to active engagement. This phase involves attempting to exploit identified vulnerabilities, mirroring the actions of potential attackers. It's a controlled exploration of how an attacker could breach a system, aiming to uncover weaknesses that might be leveraged for unauthorised access.
During this phase, Penetration Testers employ their skills and knowledge to execute strategies that exploit vulnerabilities in a safe and controlled manner. These strategies could involve using known exploits, leveraging weak authentication mechanisms, or capitalising on misconfigurations. The objective isn't to cause harm, but rather to demonstrate the potential risks and consequences of these vulnerabilities.
Maintaining access
It constitutes a pivotal phase within the Penetration Testing process, where ethical hackers go beyond initial entry and delve into understanding the potential persistence and control that an attacker could establish after breaching a system. This phase is analogous to exploring the corridors and rooms within a digital environment, understanding the extent to which unauthorised access can be maintained and manipulated.
After successfully gaining initial access, Penetration Testers aim to emulate the activities of a determined attacker seeking to maintain control over the compromised system. This involves leveraging different techniques and tools to maintain a foothold, such as creating backdoors, planting malicious code, or manipulating configurations to retain access.
Analysis and reporting
It is the culminating phase of the Penetration Testing process, where the results of the assessment are transformed into valuable insights and actionable recommendations. This phase bridges the gap between technical exploration and strategic decision-making, offering organisations a comprehensive view of their security posture and potential vulnerabilities.
During the analysis stage, Penetration Testers carefully review the data collected throughout the testing process. They consolidate findings from various phases, including vulnerabilities identified, successful exploits, and the extent of unauthorised access gained. This scrutiny involves evaluating the impact and severity of each vulnerability, considering factors such as potential consequences and the likelihood of exploitation.
The reporting phase serves multiple purposes:
1) Informed decision-making: Organisations gain a clear understanding of their security strengths and weaknesses, empowering informed decision-making regarding security investments and improvements.
2) Risk management: The report helps organisations identify and manage potential risks, enabling them to allocate resources strategically to areas most in need of attention.
3) Compliance and communication: The report can be used to show compliance with industry regulations and standards. It also facilitates communication between technical and non-technical stakeholders by presenting findings in an accessible manner.
4) Continuous improvement: The report's insights inform ongoing security efforts, allowing organisations to continuously improve their defences based on real-world vulnerabilities.
Become an expert ethical hacker with our Ethical Hacking and Penetration Testing Training.
Conclusion
Penetration Testing emerges as a cornerstone of proactive cybersecurity. This comprehensive overview has unveiled its multifaceted essence. It helped you understand What is Penetration Testing. It also helped you to identify vulnerabilities, fortify defences, and safeguard assets. Penetration Testing empowers organisations to stay one step ahead, ensuring resilience against the ever-evolving realm of cyber risks.
Frequently Asked Questions
Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 Tools and Techniques for Penetrating Testing
Tools and Techniques for Penetrating Testing
Thu 1st Jan 1970







 Top Rated Course
Top Rated Course



 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


