We may not have the course you’re looking for. If you enquire or give us a call on +08000201623 and speak to our training experts, we may still be able to help with your training requirements.
Training Outcomes Within Your Budget!
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

Step into the Ethical Hacker Roles and Responsibilities arena, where these cyber sleuths are the unsung heroes of the tech world. They’re the brainy bunch who conduct top-secret missions to find chinks in the armour of an organisation’s digital fortress. With their ethical hacking hats on, they launch fake cyber-attacks, all in the name of security. It’s a game of cat and mouse, but they’re always the cat, outsmarting the cyber mice. In this blog, we'll explore the Roles and Responsibilities of an Ethical Hacker.
Table of Contents
1) What is Ethical Hacking?
2) Who are Ethical Hackers?
3) Ethical Hacker Roles and Responsibilities
4) Essential Skills to be an Ethical Hacker
5) Where are Ethical Hackers Employed?
6) Benefits of being an Ethical Hacker
7) Conclusion
What is Ethical Hacking?
Ethical Hacking is a practice where Cyber Security professionals use hacking skills to identify vulnerabilities in systems. Networks or applications need improved security. Unlike Malicious Hackers who exploit weaknesses for personal gain, Ethical Hackers work to strengthen defences. They discover security flaws. They address them before these can be exploited by cybercriminals.
Purpose of Ethical Hacking
1) Identify Security Weaknesses: Ethical Hacking involves probing systems. Its purpose is uncovering vulnerabilities that could be exploited by attackers.
2) Prevent Data Breaches: By identifying and fixing vulnerabilities, Ethical Hackers can help prevent data breaches. These breaches could compromise sensitive information.
3) Compliance: Many industries have regulations. These regulations require regular security assessments. Ethical Hacking helps organisations comply with these standards.
4) Enhance Security Posture: Ethical Hacking leads to the development of stronger security practices and defences. This enhances the overall security posture of an organisation.
Who are Ethical Hackers?
Ethical Hackers, also called White Hat Hackers or Penetration Testers, are Cyber Security professionals. They specialise in detecting and fixing vulnerabilities that occur in systems networks and applications. These experts use their skills to help organisations secure assets.
Types of Ethical Hackers
a) In-house Ethical Hackers: These professionals are integral to an organisation’s Cyber Security team, tasked with ongoing surveillance and fortification of security measures.
b) Freelance Ethical Hackers: Operating autonomously, these hackers offer their expertise in ethical hacking to a diverse clientele and frequently participate in bug bounty programs to uncover software vulnerabilities.
c) Consultant Ethical Hackers: Allied with Cyber Security agencies, these experts execute penetration tests and conduct security evaluations for a variety of industry clients.
Unlock the world of Cyber Security – Join our Ethical Hacking Training today and defend against cyber threats ethically!
Ethical Hacker Roles and Responsibilities
Ethical Hackers play an important role in safeguarding digital environments. Responsibilities span a wide range of activities. These aim at identifying analysing and mitigating security threats. Let’s take a look at different roles and responsibilities:
Key Responsibilities
1) Penetration Testing: Execute simulated cyberattacks to uncover system vulnerabilities. Perform evaluations on both networks and applications using a blend of automated and manual testing methods.
2) Vulnerability Assessment: Scrutinise systems to pinpoint security flaws. This process entails code review, configuration checks, and architectural analysis to identify vulnerabilities.
3) Risk Analysis: Assess the severity of identified vulnerabilities and rank them according to the potential risk they pose to the organisation.
4) Security Audits: Carry out thorough security audits to measure the effectiveness of existing security controls and policies.
5) Incident Response: Aid in the investigation and resolution of security breaches. Analyse the methods of attack and establish safeguards to prevent future incidents.
6) Security Solution Development: Advise on and apply security enhancements to mitigate known vulnerabilities, which may involve applying patches, adjusting configurations, or introducing security tools.
7) Security Training: Conduct training sessions and awareness programs to inform employees about Cyber Security best practices and teach them to identify potential threats.
8) Reporting: Compile comprehensive reports documenting the discovered vulnerabilities, their possible impacts, and suggested corrective actions.
Essential Skills to be an Ethical Hacker
To excel as an Ethical Hacker, you need a robust set of technical and soft skills. Here are some essential skills that every Ethical Hacker should possess
a) Networking Proficiency: Mastery of networking principles, such as TCP/IP protocols, DNS, and firewall operations, is fundamental for identifying and exploiting network vulnerabilities.
b) Programming Acumen: Proficiency in languages like Python, Java, C++, or Ruby is critical for scripting, code analysis, and task automation to effectively target security weaknesses.
c) Operating System Knowledge: Expertise in various Operating Systems, especially Linux and Windows, is crucial as Ethical Hackers navigate through diverse computing environments to understand and breach security systems.
d) Tool Proficiency: Skilled use of hacking tools, including Metasploit, Nmap, Wireshark, and Burp Suite, is necessary for scanning, testing, and exploiting system and network vulnerabilities.
e) Cryptography Skills: A solid grasp of encryption and decryption methods, along with the ability to crack flawed cryptographic implementations, is essential for protecting and attacking sensitive data.
f) Problem-Solving Ability: Ethical hacking is a dynamic field that demands innovative and strategic problem-solving skills to foresee and neutralise potential security threats.
g) Web Application Insight: As web-based applications proliferate, understanding their security vulnerabilities—such as SQL injection, XSS, and CSRF—is increasingly important.
h) Regulatory Awareness: Knowledge of Cyber Security laws, data protection regulations, and compliance standards is imperative to ensure that ethical hacking activities remain within legal boundaries.
Learn the Metasploit Framework with our Mastering Metasploit Framework Course – Join today!
Where are Ethical Hackers Employed?
There are various departments that require Ethical Hackers whether it be a government organisation or a private firm, every company needs a Cyber Security expert who can manage the loopholes.
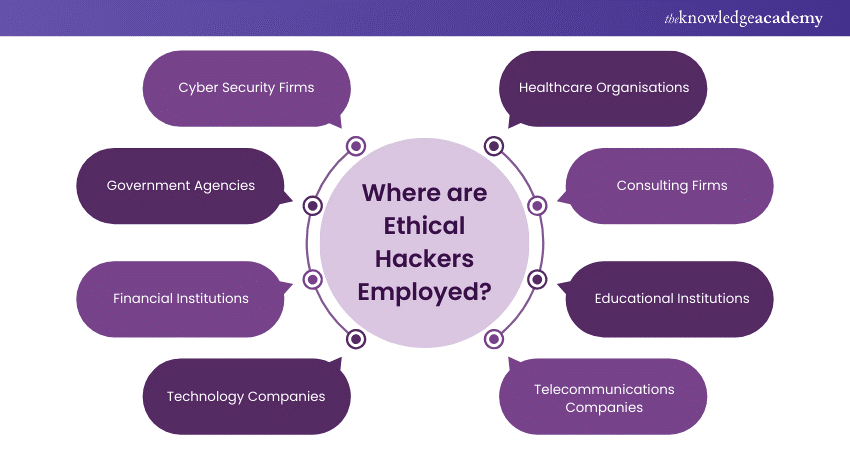
a) Cyber Security Firms: Ethical Hackers are vital to these firms, where they evaluate and enhance security solutions through penetration tests, vulnerability assessments, and threat analyses.
b) Government Agencies: These entities rely on Ethical Hackers to fortify national security by securing critical infrastructure and protecting against cyber threats.
c) Financial Institutions: Ethical Hackers are employed by banks and financial entities to safeguard transactional data, enhance online banking security, and prevent fraudulent activities.
d) Technology Companies: Ethical Hackers are crucial in ensuring the security of software, hardware, and network products developed by tech companies before market release.
e) Healthcare Organisations: To protect sensitive patient information, healthcare institutions engage Ethical Hackers to strengthen their systems against potential cyber breaches.
f) Consulting Firms: As consultants, Ethical Hackers offer specialised services such as security audits, risk assessments, and Cyber Security training to various organisations.
g) Educational Institutions: These institutions employ Ethical Hackers to educate and develop the next wave of Cyber Security professionals through teaching and research.
h) Telecommunications Companies: Ethical Hackers play a key role in maintaining the integrity of telecom networks, ensuring the security and confidentiality of customer data and communication systems.
Benefits of Being an Ethical Hacker
Pursuing a career as an Ethical Hacker comes with numerous benefits. It is an attractive field for tech enthusiasts. Here are some of the key advantages.
1) High Demand and Job Security
With the growing number of cyber threats, Ethical Hackers are in high demand. The demand translates to strong job security. Numerous employment opportunities exist across various sectors.
2) Lucrative Salaries
Ethical Hackers can expect competitive salaries. Often higher than those in many other IT professions. Their specialised skills make them valuable assets to companies driving up compensation.
3) Diverse Career Opportunities
Ethical Hackers have a range of career paths available. They can work in Cyber Security firms. They can also work in government agencies. This diversity allows them to choose roles that align with their interests and expertise.
4) Intellectual Challenge
The field of Ethical Hacking is intellectually stimulating. It requires constant learning. Ethical Hacking also involves problem-solving. This keeps the job interesting and fulfilling for those who enjoy tackling complex challenges.
5) Contribution to Society
Ethical Hackers play critical role in protecting sensitive information and maintaining Cyber Security. Their work is vital. It helps to prevent data breaches. They protect personal information and safeguard critical infrastructure.
6) Opportunity for Continuous Learning
Cyber Security is an ever-evolving field. Ethical Hackers have a chance to continually update their skills and knowledge. They stay at the forefront of technological advancements.
7) Professional Recognition
Achieving certifications like Certified Ethical Hacker (CEH) or Offensive Security Certified Professional (OSCP) can bring professional recognition. This enhances career prospects and credibility.
8) Flexible Work Environment
Many Ethical Hacking roles offer flexibility. These include opportunities for remote work. This allows for a better work-life balance and work from various locations.
Explore the intricacies of Ethical Hacking with our Ethical Hacking Training – Join today!
Conclusion
Understanding Ethical Hacker Roles and Responsibilities is crucial for appreciating their vital contribution to Cyber Security. These professionals protect organisations from cyber threats by conducting penetration tests, assessing vulnerabilities, and analysing risks. Their unique expertise and adherence to ethical standards render them indispensable in any work environment.
Frequently Asked Questions

Ethical Hacking involves authorised attempts to assess the security of systems, networks, and applications to identify vulnerabilities before malicious hackers exploit them. It's crucial for enhancing Cyber Security resilience and safeguarding sensitive data from cyber threats.

Ethical Hacking Books offer comprehensive insights, and hands-on exercises to enhance Cyber Security skills. They cover a wide range of topics, from penetration testing and exploit development to malware analysis and defensive strategies, empowering professionals to stay updated with the latest trends and techniques in the field.

The Knowledge Academy takes global learning to new heights, offering over 30,000 online courses across 490+ locations in 220 countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 17 major categories, we go the extra mile by providing a plethora of free educational Online Resources like News updates, Blogs, videos, webinars, and Interview Questions. Tailoring learning experiences further, professionals can maximise value with customisable Course Bundles of TKA.

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.

The Knowledge Academy offers various Ethical Hacking Courses including Ethical Hacking Professional, Metasploit Framework Course, etc. These courses cater to different skill levels, providing comprehensive insights into “What is a Trojan Horse?”
Our IT Security and Data Protection resources cover a range of topics related to Ethical Hacking, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your Hacking skills, The Knowledge Academy's diverse courses and informative blogs have you covered.







 Top Rated Course
Top Rated Course




 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


