We may not have the course you’re looking for. If you enquire or give us a call on +44 1344 203 999 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.
- Retired : Designing and Implementing Enterprise-Scale Analytics Solutions Using Microsoft Azure and Microsoft Power BI DP500
- Microsoft Azure Administrator AZ104
- Data Engineering On Microsoft Azure DP-203 Certification
- Microsoft Azure Security Technologies AZ500
- Designing And Implementing Microsoft DevOps Solutions AZ400

As Cloud environments continue to take over the global digital landscape, it draws new sinister and innovative Cyber threats. With these threats evolving at an alarming rate, even the strongest Cloud fortress is susceptible to breaches. This is where Microsoft Azure Tools come in, arming businesses with cutting-edge security to outsmart attackers and safeguard data.
From identity protection to real-time threat detection, these tools serve as your Cloud’s ultimate defence squad. This blog assembles a list of the seven best Azure Security Tools for you to choose from. So read on and keep your Cloud environment safe, secure and battle-ready!
Table of Contents
1) What is Azure?
2) Top 7 Azure Security Tools and Functions
3) What is the Security Assessment Tool in Azure?
4) What is Zero Trust in Azure security Tools?
5) Conclusion
What is Azure?
Microsoft Azure is a widely used Cloud platform that offers solutions like IaaS and SaaS for the purposes of backup, disaster recovery, mobile app hosting, and more. With over 600 services, it helps with efficient data processing, virtual computing, and monitoring. Microsoft Azure is cost-effective and secure and helps businesses of all sizes reduce their hardware expenses while maintaining flexibility and reliability.
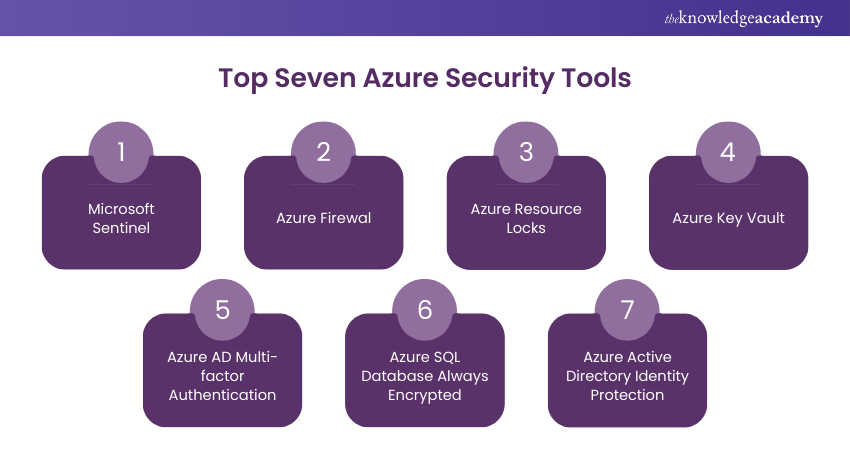
1) Microsoft Sentinel
2) Azure Firewall
3) Azure Resource Locks
4) Azure Key Vault
5) Azure Active Directory (AD) Multi-factor Authentication
6) Azure Structured Query Language (SQL) Database Always Encrypted
7) Azure Active Directory Identity Protection
Top 7 Azure Security Tools and Functions
Besides helping companies accomplish their business objectives, Azure is well known for its security services. With strong uptime, they can safely rely on the services of this cloud-native platform. It comes with a variety of tools that can help you implement and maintain security in your organisation.Here are the top Seven Azure Security Tools that you need to know about in today’s Cloud Computing world:
1) Microsoft Sentinel
Microsoft Sentinel is a cloud-native Security Information and Event Management (SIEM) solution. It helps detect, prevent, and respond to security threats across your entire organisation. Sentinel collects and analyses data from various sources, providing a comprehensive view of security issues. It uses Artificial Intelligence to identify and mitigate threats.
Best Practices:
a) Regularly Update Threat Detection Rules: Keep your detection rules up to date to identify the latest security threats. This ensures your system can effectively recognise and respond to new types of attacks.
b) Integrate All Relevant Data Sources: Connect all your data sources to Sentinel for a comprehensive security overview. This helps in detecting patterns and anomalies across your entire environment.
c) Use Automated Response Playbooks: Implement automated responses for common threats to reduce response time. This ensures quick action on detected threats, minimising potential damage.
2) Azure Firewall
It is a cloud-based network security service that safeguards your Azure Virtual Network resources. It offers both application and network-level filtering rules, helping to block malicious traffic and prevent unauthorised access. Azure Firewall is highly available and can scale to meet your network traffic needs. It provides logging and analytics to monitor and improve your security posture.
Best Practices:
a) Define Clear Traffic Filtering Rules: Create specific rules to control traffic flow and block malicious activity. This helps ensure only legitimate traffic can access your resources.
b) Enable Logging for All Activities: Turn on logging to track all firewall activities and identify any suspicious behaviour. Logs provide valuable insights for auditing and troubleshooting.
c) Regularly Review and Update Rules: Periodically check and update the firewall rules to live up to new threats. This keeps your security measures current and effective.
3) Azure Resource Locks
Azure Resource Locks help prevent accidental deletion or modification of your critical resources. By applying locks, you can ensure that important resources are protected from unintentional changes. ReadOnly and CanNotDelete are the two types of locks. These locks provide a layer of security by enforcing restrictions on resource modifications.
Best Practices:
a) Apply Locks to Critical Resources: Use locks to safeguard essential resources from accidental changes. This prevents costly mistakes that could disrupt your operations.
b) Use ReadOnly Locks for Sensitive Data: Implement ReadOnly locks on resources that should not be modified. This ensures that the data remains unchanged and secure.
c) Regularly Review Lock Configurations: Check your lock settings periodically to ensure they meet your security needs. Adjust locks as necessary to protect your most important resources.
4) Azure Key Vault
It is a cloud service for storing and managing sensitive information like keys, secrets, and certificates. It helps safeguard cryptographic keys used by cloud applications and services. Key Vault simplifies key management and ensures that your secrets are protected with Hardware Security Modules (HSMs). It also enables secure access to your secrets and keys using managed identities.
Best Practices:
a) Regularly Rotate Keys and Secrets: Change your keys and secrets frequently to enhance security. Regular rotation reduces the risk of exposure and unauthorised access.
b) Set Up Access Policies: Define who can manage and use your keys and secrets. Access policies ensure only authorised users have the necessary permissions.
c) Monitor Access and Usage: Use Azure monitoring tools to track who is accessing your keys and secrets. This helps detect and respond to suspicious activities promptly.
Gain expertise in developing, testing, and maintaining Azure solutions in our Developing Solutions for Microsoft Azure AZ-204 Certification - Sign up now!
5) Azure AD Multi-factor Authentication
Authentication Azure AD Multi-factor Authentication (MFA) adds an additional layer of security to your user sign-ins. It requires users to give two or more verification methods, such as a a mobile app notification or password. MFA helps protect against credential theft and unauthorised access. It's an essential tool for strengthening the security of user accounts.
Best Practices:
a) Enable MFA for All Users: Ensure that every user in your organisation uses MFA. This greatly reduces the risk of account breaches.
b) Regularly Review Authentication Methods: Check and update the verification methods to keep them effective and secure. Ensuring the latest methods are used helps maintain strong protection.
c) Educate Users on MFA Importance: Inform your users about the Microsoft Azure Benefits of MFA and how to use it properly. Education ensures users understand and effectively use this security measure.
6) Azure SQL Database Always Encrypted
Azure SQL Database Always Encrypted helps protect sensitive data by ensuring that it remains encrypted during storage and transit. This feature allows you to encrypt confidential data within your database without revealing the encryption keys to the database system.
Only authorised applications and users can access the encrypted data. 'Always Encrypted' ensures that sensitive information, such as credit card numbers and personal identifiers, is secure.
Best Practices:
a) Encrypt All Sensitive Data Fields: Make sure to encrypt fields containing sensitive information. This protects your most valuable data from unauthorised access.
b) Use Strong Encryption Algorithms: Apply robust encryption methods to secure your data. Strong algorithms provide better protection against decryption attempts.
c) Regularly Rotate Encryption Keys: Change encryption keys periodically to enhance security. Key rotation helps prevent long-term exposure of encrypted data.
Ready to dive into Azure? Get the Microsoft Azure Fundamentals PDF now and begin preparing for your certification exam with ease.
7) Azure Active Directory Identity Protection
Azure Active Directory Identity Protection helps detect and respond to identity-based risks. It uses Machine Learning (ML) to identify suspicious activities, such as unusual sign-in attempts and potential account compromises. Identity Protection provides detailed reports and alerts to help you address these risks promptly. It also offers automated responses to mitigate identified risks.
Best Practices:
a) Enable Risk-based Conditional Access Policies: Use policies that adapt based on detected risks to control access. This ensures that legitimate users can access sensitive resources.
b) Regularly Review Identity Protection Reports: Check the reports and alerts frequently to stay informed about potential threats. Regular reviews help you respond quickly to any issues.
c) Educate Users on Suspicious Activities: Teach your users to recognise and report unusual account behaviour. User awareness helps in early detection and prevention of security incidents.
Gain expertise in deploying Azure Virtual Desktop for ideal remote work solutions in our AZ-140 Configuring and Operating Azure Virtual Desktop Course - Register now!
Explore the Features and Importance of Azure Security Tools
Let’s dive into the many exciting features and the growing importance of Azure security services and tools to better understand the innovative nature of this technology
How to Choose the Best Azure Security Tools?
Selecting the right Azure Security Tools is crucial for protecting your cloud environment. Here are five simple tips to help you make the best choice for your organisation.
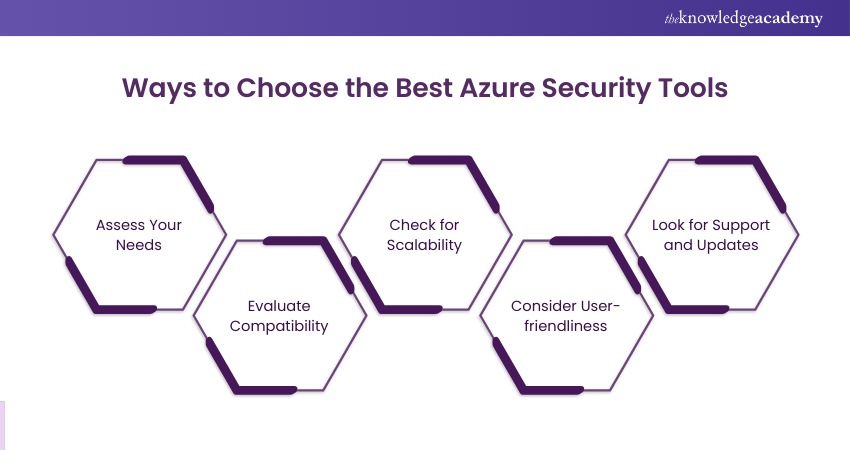
a) Assess Your Needs: Identify the specific security requirements of your organisation. Consider factors like data protection, network security, and User Access Management. Choosing tools that address these needs ensures comprehensive security coverage.
b) Evaluate Compatibility: Ensure the security tools you choose are compatible with your existing Azure infrastructure. Tools that integrate seamlessly with your current setup will be easier to implement and manage. Compatibility minimises disruption and maximises efficiency.
c) Check for Scalability: Choose security tools that can grow with your organisation. As your business expands, your security needs will also increase. Scalable tools can handle increased data, users, and traffic without compromising performance.
d) Consider User-friendliness: Opt for security tools that are easy to use and understand. User-friendly tools simplify training and reduce the likelihood of errors. This ensures that your team can manage and utilise the tools.
e) Look for Support and Updates: Select tools from vendors that offer strong customer support and regular updates. Continuous support and updates are essential for addressing new security threats and maintaining tool effectiveness. Reliable vendor support ensures your security tools remain up-to-date and functional.
Learn core Azure services with our Microsoft Azure Fundamentals AZ-900 Certification -Join today!
What is the Importance of Azure Security Tools?
Azure Security Tools are essential for maintaining a secure and compliant cloud environment. Here are five reasons why these tools are crucial for your organisation.
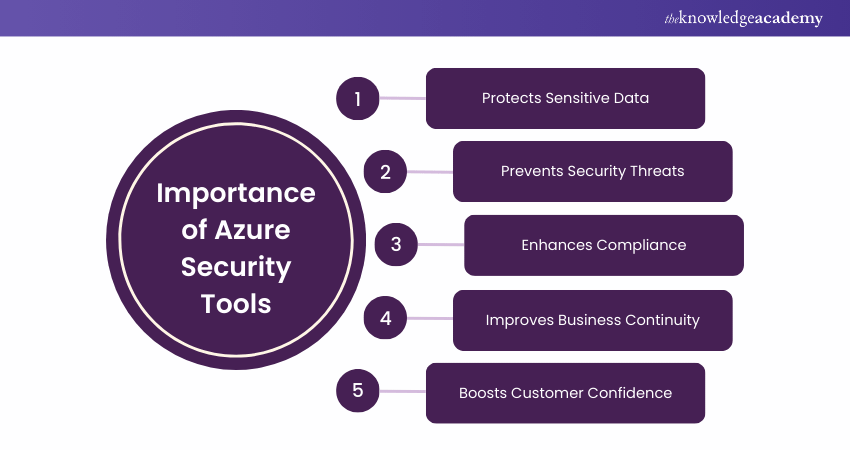
a) Protects Sensitive Data: Azure Security Tools help safeguard your data from unauthorised access. Protecting data is crucial for maintaining privacy and compliance with regulations. Effective data protection builds trust with customers and stakeholders.
b) Prevents Security Threats: These tools identify and mitigate security threats, such as malware and phishing. Proactively addressing threats minimises the risk of security incidents. Preventing threats ensures the integrity and availability of your systems.
c) Enhances Compliance: Using this tool helps you comply with industry standards and legal requirements. Compliance ensures your organisation meets necessary security and privacy regulations. Adhering to regulations avoids legal penalties and enhances your reputation.
d) Improves Business Continuity: It protects your systems from disruptions caused by cyber-attacks and other threats. Maintaining business continuity ensures your operations run smoothly without interruptions. Consistent operations support business growth and customer satisfaction.
e) Boosts Customer Confidence: Implementing robust security measures increases customer trust in your organisation. Customers feel safer knowing their data is protected by effective security tools. High customer confidence can lead to increased loyalty and business success.
Acquire expertise in Azure security with our Microsoft Azure Security Technologies AZ500 Course – Join today!
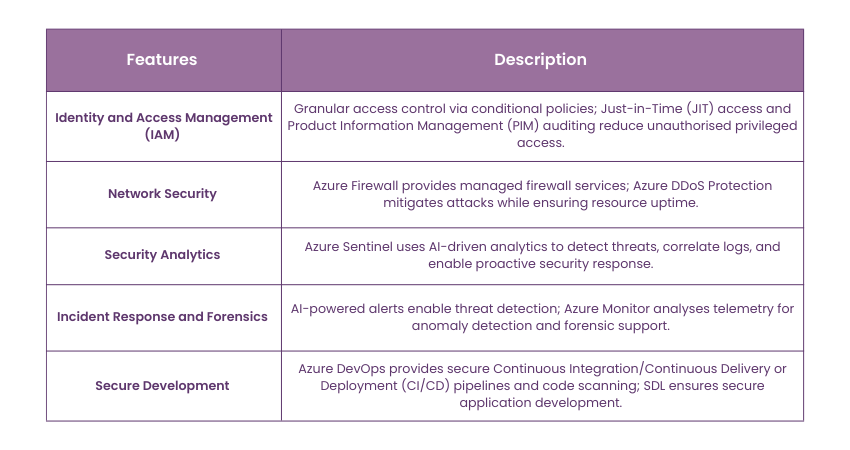
What are the Features of Azure Security Tools
Here are the features that make Azure Security Tools so important:
How do Microsoft Azure Security Tools Protect Your Cloud?
Here’s how Microsoft Azure Security Tools help protect your Cloud environment:
1) You can identify and respond to attacks in real-time with security improvement suggestions.
2) Microsoft Defender for Cloud protects Cloud apps, defends against modern threats, and reduces risks in multi-cloud and hybrid setups.
3) Azure Security Center delivers threat detection, vulnerability scanning, and Security Policy Management.
4) You can get a unified security view across Azure, Amazon Web Services (AWS), Google Cloud, and hybrid environments.
5) Context-aware security helps prioritise critical risks and manage real-time access.
6) Azure AD improves secure identity and access control with conditional access, Multi-factor Authentication (MFA) and Privileged Identity Management.
7) A unified XDR solution helps detect, prevent, and respond to attacks across multi-cloud workloads.
8) Azure Key Vault securely stores keys and secrets, while Azure Firewall and Distributed Denial-of-service (DDoS) Protection defend against network threats.
9) Azure Sentinel provides smart security analytics and automated responses for quick threat detection.
10) You can strengthen App Development security with central insights across multiple pipelines and Cloud platforms.
What is the Security Assessment Tool in Azure?
It's a feature that helps organisations assess their Cloud security posture and identify potential vulnerabilities and compliance issues. It provides recommendations based on the best practices and can help organizations plan their security strategy effectively.
What is Zero Trust in Azure Security Tools?
Azure's Zero Trust security model assumes that no user, device, or network is inherently trustworthy. Every access request is verified, and activities are continuously monitored. It prioritises identity verification, authentication, and ongoing security checks to ensure protection regardless of resource location or network boundaries.
Conclusion
Azure is a dynamic cloud platform that can help your company in various ways with consistent quality and efficiency. Remember, securing your Cloud environment is not optional in today's digital landscape. With the Azure Security Tools highlighted in this blog, you can protect your data, detect threats, and control your digital assets. This will help you build a resilient, future-proof security strategy for your business.
Gain skills in managing cloud services with our Microsoft Azure Administrator AZ104 Course – Join now!
Frequently Asked Questions
Are Azure Security Tools Suitable for Businesses of all Sizes?

Yes, Azure Security Tools are suitable for businesses of all sizes. They offer scalable solutions that can be customised to fit small startups as well as large enterprises. This flexibility ensures that every business can benefit from improved security.
Can Azure Security Tools Help with Regulatory Compliance Requirements?

Yes, Azure Security Tools can help with regulatory compliance requirements. They provide features that ensure your data and operations meet industry standards and legal requirements. Using these tools helps businesses avoid legal issues.
What are the Other Resources and Offers Provided by The Knowledge Academy?

The Knowledge Academy takes global learning to new heights, offering over 3,000 online courses across 490+ locations in 190+ countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 19 major categories, we go the extra mile by providing a plethora of free educational Online Resources like News updates, Blogs, videos, webinars, and interview questions. Tailoring learning experiences further, professionals can maximise value with customisable Course Bundles of TKA.
What is The Knowledge Pass, and How Does it Work?

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.
What are Related Courses and Blogs Provided by The Knowledge Academy?

The Knowledge Academy offers various Microsoft Azure Certification, including the Microsoft Azure Fundamentals AZ-900 Certification, Microsoft Azure Security Technologies AZ500 Course, and Microsoft Azure Administrator AZ104 Course. These courses cater to different skill levels, providing comprehensive insights into Azure ExpressRoute.
Our Microsoft Technical Blogs cover a range of topics related to Azure, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your knowledge on Azure, The Knowledge Academy's diverse courses and informative blogs have got you covered.
Upcoming Microsoft Technical Resources Batches & Dates
Date
 Microsoft Azure Fundamentals AZ-900 Certification
Microsoft Azure Fundamentals AZ-900 Certification
Fri 11th Apr 2025
Fri 13th Jun 2025
Fri 8th Aug 2025
Fri 26th Sep 2025
Fri 21st Nov 2025






 Top Rated Course
Top Rated Course



 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


