We may not have the course you’re looking for. If you enquire or give us a call on + 800 908601 and speak to our training experts, we may still be able to help with your training requirements.
Training Outcomes Within Your Budget!
We ensure quality, budget-alignment, and timely delivery by our expert instructors.
In the evolving field of Cyber Security, two practices frequently find themselves in the spotlight - Ethical Hacking and Penetration Testing. While these approaches are seen as two sides of the same coin, they boast some key differences. While Ethical Hacking is like a detective wielding broader techniques to detect hidden threats, Penetration Testing is a targeted laser-focused operation that zeroes in on vulnerabilities in security frameworks. This blog highlights the winning features in the Ethical Hacking vs Penetration Testing debate. Read on and understand how they complement each other in fortifying your defences in the current environment of multiplying Cyber threats.
Table of Contents
1) What is Ethical Hacking and Penetration Testing?
a) Overview of Ethical Hacking
b) Overview of Penetration Testing
2) Ethical Hacking vs Penetration Testing: Key differences
3) Conclusion
What is Ethical Hacking and Penetration Testing?
Ethical Hacking and Penetration Testing might seem interchangeable. However, both have their respective use cases for keeping your systems and networks safe. Here’s an overview on both terms:
Overview of Ethical Hacking
Ethical Hacking (also known as White Hat Hacking) is a legal and authorised practice of identifying vulnerabilities in computer systems, applications or networks. Ethical Hackers use their skills to uncover security weaknesses that malicious hackers could exploit. The core objective is to assess and strengthen an organisation's security posture by simulating real-world cyber-attacks.
Overview of Penetration Testing
Penetration Testing is a security test in which an organisation hires a certified professional to assess the strength of its Cyber Security defences. These tests are typically performed through on-site audits of the organisation in question, and the tester is granted access to a certain amount of privileged information.

There are different types of penetration tests which focus on specific aspects of an organisation’s security perimeter. These tests include:
a) External Network Tests: These look for vulnerabilities and security issues in an organisation’s servers, devices, hosts, and network services.
b) Internal Network Tests: These tests assess the damage an attacker could do when accessing an organisation’s internal systems.
c) Web application tests look for insecure development practices in designing, coding, and publishing software or a website.
d) Wireless Network Tests: These assess vulnerabilities in wireless systems, including rogue access points, Wi-Fi, and weak encryption algorithms.
e) Phishing Penetration Tests: These tests assess employees’ susceptibility to scam emails.
Penetration Testing is typically carried out at regular, set times, when the organisation makes significant changes to its networks or applications.
Try our Ethical Hacking Training and learn to legally bypass the security of systems!
Ethical Hacking vs Penetration Testing: Key Differences
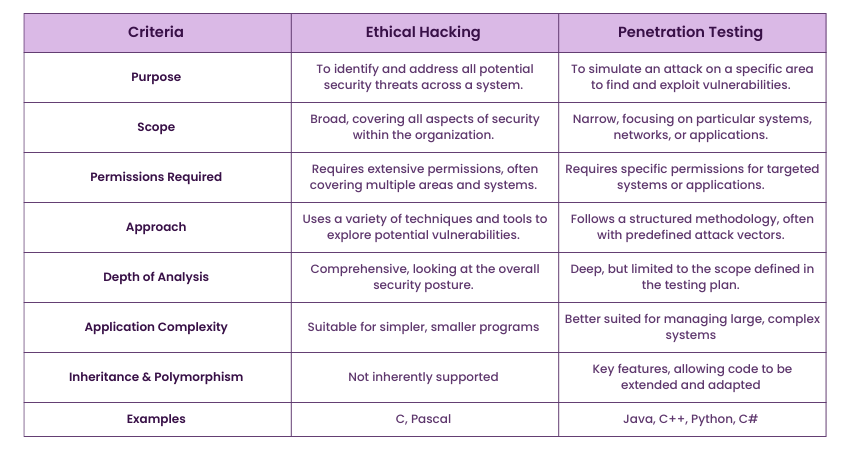
While Ethical Hacking and penetration Testing share the common goal of identifying security weaknesses, they differ in several aspects. Some of these aspects include their scope and adherence to legal obligations. Some such differences are summarised below:
Curious about how ethical hackers safeguard the digital world? Discover What is Ethical Hacking? in our latest blog. Click here to dive in and learn!
Ethical Hacking vs Penetration Testing: Scope
Ethical Hacking emphasises the identification of vulnerabilities in systems and networks with the aim of improving security measures. Ethical Hackers proactively search for weaknesses that malicious actors could potentially exploit.
On the other hand, Penetration Testing focuses on assessing the effectiveness of existing security controls, aiming to simulate real-world attacks and validate the system's resilience against such attacks. Penetration Testers assess the organisation's defences, identifying potential vulnerabilities and their impact.
The scope of Ethical Hacking and Penetration Testing professionals may vary depending on their respective goals. The former is often more extensive and comprehensive, striving to uncover vulnerabilities across the entire network. It involves a wide range of testing methodologies and tools to identify weaknesses. Penetration Testing often has a narrower scope, stressing the specific targets or areas within the system.

Ethical Hacking vs Penetration Testing: Legality
Both Ethical Hackers and Penetration Testers are authorised individuals that require consent from the organisation or system owner. They are conducted with stakeholders' explicit permission and cooperation to ensure compliance with legal and ethical boundaries.
Legal considerations are crucial for both the Ethical Hacking and Penetration Testing process. Adherence to applicable laws and regulations is paramount to preventing unintended consequences or legal implications. Ethical Hackers and Penetration Testers must understand the legal frameworks and requirements governing their activities, such as data protection and privacy laws.
Documentation and clear communication with stakeholders play a significant role in ensuring compliance. Ethical Hacking and Penetration Testing professionals should maintain thorough records of their activities, findings, and recommendations. Clear and transparent communication with the organisation and relevant stakeholders helps establish a mutual understanding of the testing objectives, processes, and potential risks.
Adhering to authorisation and legality requirements allows Ethical Hacking and Penetration Testing experts to provide valuable insights to organisations while maintaining ethical standards and minimising potential negative impacts.
Learn the basics of Ethical Hacking with our Ethical Hacking Professional Course! Sign up now!
Conclusion
Ethical Hacking vs Penetration Testing is a well-debated topic among organisations seeking to keep themselves digitally safe. Both are crucial components of a robust Cybersecurity strategy. Understanding the differences between these practices will help you make informed decisions to strengthen your defences and protect against evolving threats.
Try our Mastering Metasploit Framework Course and use Metasploit in Penetration Testing!
Frequently Asked Questions

The career path of a penetration tester includes the following steps:
a) Signing up for a related baccalaureate degree in IT and Cyber Security
b) Gain foundational skills in college
c) Earn professional certifications
d) Find a Penetration Testing job
e) Continue learning and staying updated in industry trends

The five stages of Pentesting are reconnaissance, scanning, vulnerability assessment, exploitation, and reporting.

The Knowledge Academy takes global learning to new heights, offering over 30,000 online courses across 490+ locations in 220 countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 17 major categories, we go the extra mile by providing a plethora of free educational Online Resources like News updates, Blogs, videos, webinars, and interview questions. Tailoring learning experiences further, professionals can maximise value with customisable Course Bundles of TKA.

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.

The Knowledge Academy offers various Ethical Hacking Courses, including Ethical Hacking Professional. These courses cater to different skill levels, providing comprehensive insights into Ethical Hacker Roles and Responsibilities.
Our IT Security & Data Protection blogs covers a range of topics related to Ethical Hacking Professional, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your IT Security and Data Protection, The Knowledge Academy's diverse courses and informative blogs have you covered.
Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 Ethical Hacking and Penetration Testing Training
Ethical Hacking and Penetration Testing Training
Fri 28th Mar 2025
Fri 23rd May 2025
Fri 4th Jul 2025
Fri 5th Sep 2025
Fri 5th Dec 2025







 Top Rated Course
Top Rated Course



 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


