We may not have the course you’re looking for. If you enquire or give us a call on + 1-866 272 8822 and speak to our training experts, we may still be able to help with your training requirements.
We ensure quality, budget-alignment, and timely delivery by our expert instructors.
Have you ever pondered the mechanism that enables devices within a computer network to exchange data and interact? The key lies in the concept of network topology. Network topology is the structure of cables, nodes, and various elements constituting the network’s infrastructure. Among the prevalent network topologies is the Ring Network Topology, distinguished by its circular configuration that interlinks all devices in the network.
This architectural marvel, a cornerstone of network design, features a circular layout where each node is a crucial link in the communication chain. Join us as we circle through Ring Network Topology's fundamentals, intricacies, and technicalities, providing you with a well-rounded understanding of this elegant networking framework.
Table of Contents
1) What is a Ring Topology?
2) How does Ring Topology Work?
3) Applications of Ring Topology?
4) Advantages of a Ring Topology
5) Disadvantages of a Ring Topology
6) Devices using Ring Topology
7) Data transmission steps in Ring Topology
8) Conclusion
What is a Ring Topology?
Ring Topology is a network configuration where devices are interconnected in a circular pattern, allowing them to communicate sequentially with their immediate network neighbours. This topology is noted for its efficiency and capacity to manage substantial loads, outperforming bus topology. Typically, Ring Topologies are unidirectional, with data packets circulating in a single direction, though bidirectional variants also exist, allowing two-way data flow.
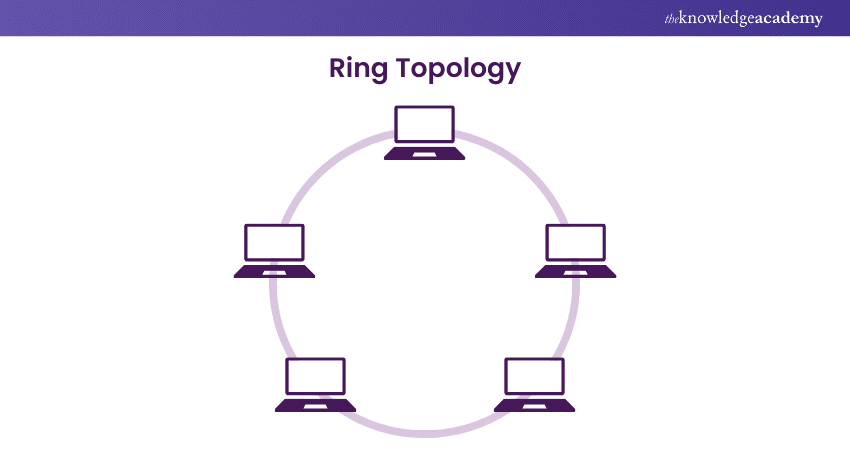
Employed in both Local Area Networks (LANs) and Wide Area Networks (WANs), Ring Topology does not rely on a central hub. The connectivity between computers in a Ring Network is determined by the type of network card installed, which dictates whether an RJ-45 network cable or a coaxial cable is used. This topology offers notable benefits, such as the simplicity of installation and the straightforwardness of troubleshooting.
However, Ring Topology has vulnerabilities; a single non-functioning node can disrupt the entire network. Some networks adopt a dual-ring design to mitigate this risk, enabling data transmission in clockwise and counter-clockwise directions. This redundancy ensures a secondary transmission path is available should the primary one fail; hence, these configurations are termed redundant ring structures. Those studying for the CCNA certification will benefit from understanding Ring Topology due to its importance in network design.
How does Ring Topology Work?
Ring Topology is a network configuration where each node is connected to two others, forming a circular data path. Here’s a refined explanation of how data transmission occurs in a Ring Topology:
a) Token circulation: When no data is being sent, a token, which is a special data packet, circulates around the ring. The network can operate at speeds ranging from 16 Mbps to 100 Mbps.
b) Token acquisition: When a node wants to send data, it captures the circulating empty token, fills it with the data frame, and includes the destination node’s MAC address and identifier.
c) Data transmission: This filled token is then passed along the ring to the next node.
d) Token reception: Each node examines the incoming token to see if it is the intended recipient. If so, it copies the data from the token, marks the token as read, and forwards it to the next node.
e) Data delivery: This process continues until the token reaches its intended destination.
f) Acknowledgement: Once the original sender node gets the token back and sees that the data has been read, it removes it from the token, rendering it empty again.
g) Token reuse: The now empty token is released back into the ring for any node that needs to transmit data.
h) Fault tolerance: If a node fails or is not transmitting data, and if the network supports a dual-ring structure, the data can be sent in the reverse direction to reach its destination.
This system ensures efficient and orderly data transmission, with the token acting as a ‘baton’ that nodes pass to communicate within the network. These processes are crucial for understanding key responsibilities outlined in a network engineer job description.
Do you want to learn how you can design, install and support business critical network switches? Register now for our CCNA Certification Course!
Importance of Ring Topology
Ring Topology is chosen for its distinct characteristics that align with specific network requirements and constraints. Here, Ring Topology is used, considering various factors:
Factors influencing topology choice:
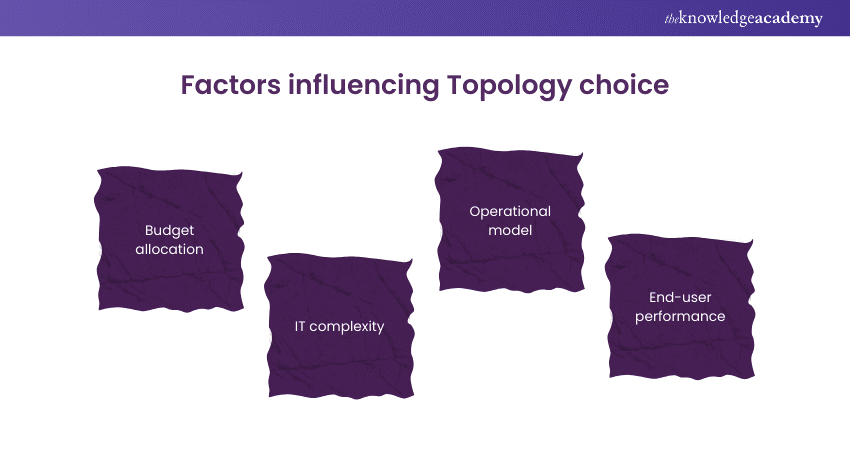
a) Budget allocation: Financial resources available for network setup and maintenance.
b) IT complexity: The intricacy of the existing IT infrastructure.
c) Operational model: How the organisation functions and its networking needs.
d) End-user performance: The expected level of network service for the end-users.
Reasons for selecting ring topology:
a) Minimal collision risk: The unidirectional data flow in a Ring Topology greatly reduces the chances of data collisions.
b) No central control: It eliminates the need for a central network server to manage data transmission, simplifying the network structure.
c) Speed: Data transmission is swift, facilitating faster communication between nodes.
d) Cost-effectiveness: Ring Topology networks are economical, making them a budget-friendly option.
e) Ease of expansion: Adding new nodes or making changes is straightforward, simplifying network administration.
These reasons highlight the practicality of Ring Topology in scenarios where budget, simplicity, and efficient data handling are key considerations. Understanding these aspects is key to appreciating the importance of CCNA, as it helps professionals make informed network design decisions.
Applications of Ring Topology
Ring Topology is versatile and finds application in various network configurations, including both Local Area Networks (LANs) and Wide Area Networks (WANs). Here’s a refined description of its applications:
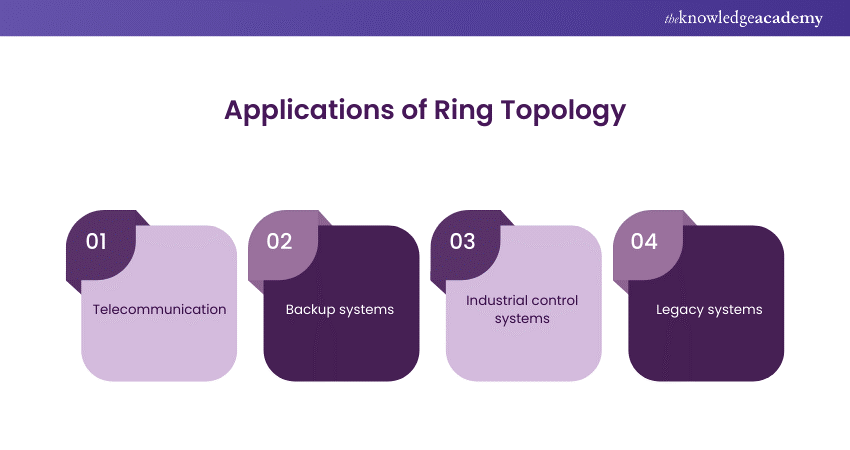
a) Telecommunications: Due to its high bandwidth and fault tolerance capabilities, it is widely used in the telecommunications sector, particularly in Synchronous Optical Network (SONET) fibre optic networks.
b) Backup systems: Organisations often implement Ring Topology as a secondary, fail-safe network arrangement to support their primary network infrastructure.
c) Industrial control systems: In industrial settings, Ring Topology connects devices like sensors, controllers, and actuators. Its reliability ensures uninterrupted communication and control by rerouting data in case of a break.
d) Legacy systems: While Ethernet dominates modern networks, older systems might still use ring topology. Upgrading these systems is often not cost-effective, but ring topology remains functional for specific purposes.
Overall, Ring Topology’s ability to handle high-speed data transfer and provide a reliable backup makes it a practical choice for various networking needs. Understanding the difference between CCNA and CCNA Security improves the effective use of Ring Topology by covering different network management and security aspects.
Do you want to learn the essentials of interconnecting CISCO Networking Devices? Sign up now for our Interconnecting Cisco Networking Devices Part 1 Course!
Advantages of a Ring Topology
Ring Topology offers several benefits, which are listed below:
a) Unidirectional data flow: Data moves in a single direction, minimising the likelihood of data packet collisions.
b) Decentralised management: No central node or server needs to manage the connectivity between workstations.
c) High-speed transfers: Workstations can exchange data at high speeds.
d) Scalability: Adding more workstations doesn’t significantly affect the network’s performance.
e) Efficiency under load: It outperforms bus topology, especially under heavy network traffic.
Disadvantages of a Ring Topology
Here is the list of Disadvantages:
a) Dependency on continuity: The biggest drawback is the dependency on the integrity of the ring; if one workstation or connection fails, it can disrupt the entire network. Implementing a dual ring or switches can mitigate this risk.
b) Throughput delays: Since data must pass through every workstation, it can be slower than in a star topology.
c) Higher costs: The hardware required to connect each workstation, such as network interface cards and switches, is typically more costly than those used in Ethernet networks.
d) Network fragility: The addition, movement, or reconfiguration of devices within the ring can potentially disrupt network operations.
While Ring Topology is efficient and scalable, it requires careful management to ensure network resilience and optimal performance.
Learn in-depth about GNS3 Architecture with our GNS3 Training – Sign up now!
Devices using Ring Topology
Here are a few examples of Ring Topology Devices:
a) Token Ring: This popular network technology employs Ring Topology for Local Area Networks (LANs).
b) Fiber Distributed Data Interface (FDDI): Utilised mainly for high-speed data transfer over fibre optic cables in a Ring Topology.
Data Transmission Steps in Ring Topology
Here is how you can transmit data in Ring Topology
1) Initiation: You start the data transmission from your device.
2) Propagation: The data packet moves sequentially along the ring's path from one device to the next.
3) Reception check: Each device examines the incoming data to determine if it is the addressee.
a) If not, the data is sent onward to the subsequent device in the ring.
4) Receipt and processing: Once the data arrives at the correct recipient, it is accepted and processed.
This process ensures that data circulates the ring until it reaches its intended destination.
Conclusion
The Ring Network Topology is more than just a configuration; it’s a symphony of interconnected devices playing in unison to orchestrate seamless data transmission. As we’ve journeyed through the loops of information, we’ve seen its strengths in creating harmonious networks that are both resilient and efficient. Whether in small-scale setups or vast metropolitan networks, the Ring Topology remains a testament to the power of connectivity in a circular form, proving that every node, no matter how small, plays a vital role in the bigger picture.
Learn how you can navigate and use the Meraki Dashboard with our Cisco Meraki Training- Join now!
Frequently Asked Questions

Yes, Ring Topology can support high-speed data transfers due to its dedicated pathways and reduced chances of collision, ensuring swift and reliable communication.

Troubleshooting a Ring Network is straightforward since faults can be detected and isolated quickly, minimising downtime and maintaining network integrity.

The Knowledge Academy takes global learning to new heights, offering over 30,000 online courses across 490+ locations in 220 countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 17 major categories, we go the extra mile by providing a plethora of free educational Online Resources like News updates, Blogs, videos, webinars, and interview questions. Tailoring learning experiences further, professionals can maximise value with customisable Course Bundles of TKA.

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.

The Knowledge Academy offers various CCNA Training, including Cisco Packet Tracer Course, CCNP Collaboration Training Course, and Cisco Meraki Training Course. These courses cater to different skill levels, providing comprehensive insights into Networking Career methodologies.
Our IT Infrastructure & Networking Blogs cover a range of topics related to Networking, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your Networking skills, The Knowledge Academy's diverse courses and informative blogs have got you covered.
Upcoming IT Infrastructure & Networking Resources Batches & Dates
Date
 CCNA Certification
CCNA Certification
Mon 17th Mar 2025
Mon 26th May 2025
Mon 14th Jul 2025
Mon 22nd Sep 2025
Mon 24th Nov 2025
Mon 8th Dec 2025







 Top Rated Course
Top Rated Course



 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


