Why Ethical Hacking is Important?
Find Organisations’ Weakness
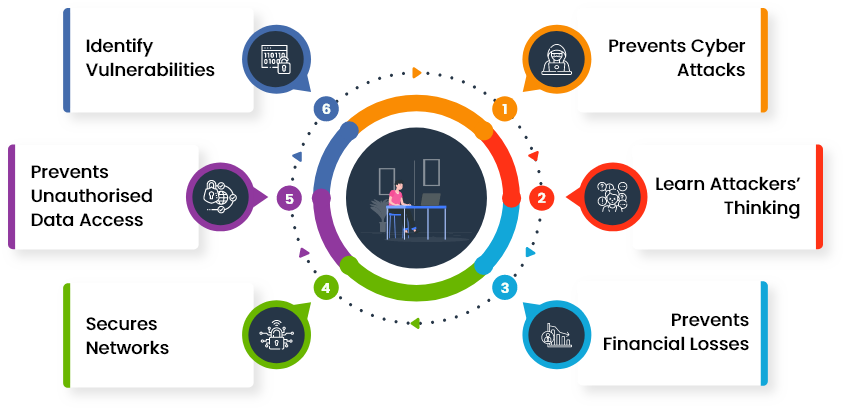
Ethical Hacking helps to determine the weaknesses of an organisation’s security system and fix them before becoming a concern.
Secure Important Data
Ethical Hacking is utilised to shield crucial data from rivals. It works to protect the computer from hackers to important data.
Fix Attacks Before Occurring
Ethical Hackers can think like an attacker, find the probable access points, and resolve them before any possible attack.
Ethical Hacking Training Overview
Ethical Hacking is the legal activity of bypassing system security in order to detect potential data breaches and network risks. Ethical Hacking practices help organisations to identify the vulnerabilities of their networks and systems and build solutions to prevent data breaches. It also assists individuals to prevent their personal information and financial loss from malicious attacks.
Our popular Ethical Hacking Training courses cover vital skills to learners about executing effective penetration testing and assessing how susceptible organisations are to hacking. Our highly skilled and experienced trainer will conduct Ethical Hacking training and help learners foster specific skills to help them develop and succeed in their careers.
Benefits Of Ethical Hacking
Our Available Delivery Methods




Online Instructor-Led Training


Online Self-Paced Training


Onsite Training
Best Selling Courses in United Kingdom
Popular Career Advancement Courses
Ethical Hacking Professional
Duration: 2 Days
All Delivery Methods: Available
Mastering Metasploit Framework
Duration: 1 Day
All Delivery Methods: Available
Ethical Hacking and Penetration Testing Training
Duration: 1 Day
All Delivery Methods: Available
Ethical hacking and network defence training
Duration: 1 Day
All Delivery Methods: Available
Kali Linux Fundamentals
Duration: 1 Day
All Delivery Methods: Available
Tools And Techniques For Penetrating Testing
Duration: 2 Days
All Delivery Methods: Available
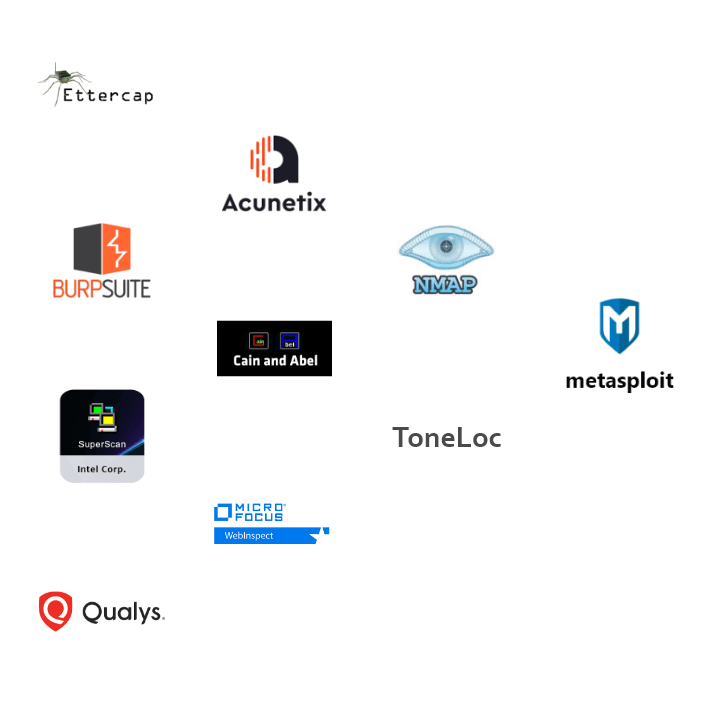
Ethical Hacking Techniques
Ethical hackers utilise the same methods to hack that malicious actors employ to attack corporations and individual professionals. Ethical hackers use a form of reverse engineering to visualise systems that can compromise operational and business data. White hat hackers or ethical hackers serve their client's behalf and use various tools and techniques to assess their systems' vulnerability points. Here are the main hacking techniques:
- Bait and Switch
- Eavesdropping
- Cookie Theft
- Fake WAP
- ClickJacking Attacks
- Waterhole Attacks
- Phishing
- Denial of Service (DoS\DDoS)
Ethical Hacking Process

Fact and Figures

100
+Courses Running Daily

490
+Locations Worldwide

2
M+Professionals Trained
Transforming Organisations and Individuals Across the Globe
"Over 150K+ Satisfied Customers"

What Professional Hackers Do?
Professional hackers or ethical hackers utilise their abilities to examine personal and organisational IT system vulnerabilities to prevent any security breaches and data leaks. An ethical hacker will try to avoid system security and find and disclose weak points that an unethical hacker could exploit, investigate and record the findings, and discuss their plans and security improvements with IT and management teams. Ethical hackers will also give feedback and verification as and when an organisation improves security systems. The main goal of ethical hacking is to examine and ensure the safety of any system and network infrastructure. Additionally, they give remediation advice and help organisations in various ways, including:
- Finding Vulnerabilities of an Organisation’s Security System
- Showing Methods Used by Cybercriminals and Devising Ways to Prevent Them
- Helping Organisations to Prepare for and Handle Cyberattacks
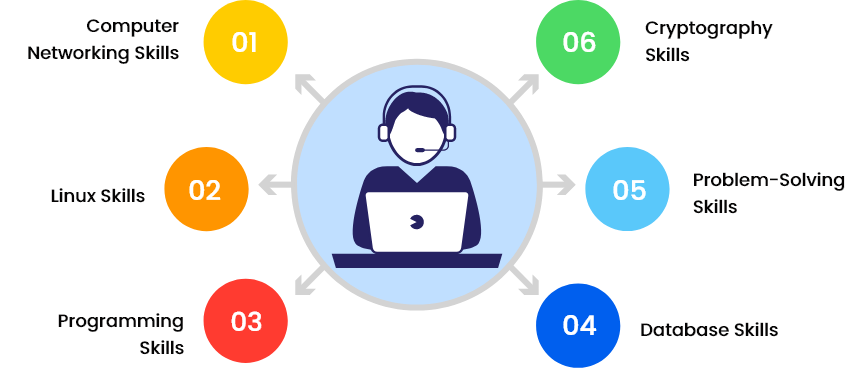
Skills for Ethical Hacker
Why We are Best for You?
We help you quench your thirst for knowledge by providing you with our specially tailored certifications. Our highly qualified instructors, dedicated staff, and 24/7 available helpline are the main reasons why we're the go-to training provider for you.

Best Price Guarantee
You won't find better value in the marketplace. If you find a lower price, send us the offer, and we'll beat it.

Guaranteed to Run
Our training courses are 100% guaranteed to run on dates provided, whether they are classroom, virtual, or in-house.

Highly Experienced Staff
Our support staff and instructors have years of experience in meeting the specific needs of our clients and delivering exceptional quality.
Top Ethical Hacking Tools to Look Out
Loved by Businesses and Individuals Across the Globe

I had completed the ethical hacking professional training course yesterday. The course content was useful and informative for beginners, and in my opinion, it was an excellent course for enhancing my knowledge. I have no words to praise my trainer. The only thing I can say is that he was the best instructor I have trained with. She made it easy for me to grab the content with her unique and friendly teaching style.

Skye Davidson
Ethical Hacking Analyst

I attended this Mastering Metasploit Framework course from the knowledge academy and had a great experience. I got a great trainer and explicit material for my training course. The trainer showed his knowledge and understanding of the topics with suitable examples and detailed explanations. This was the excellent service I have ever experienced. I would definitely recommend this course to my friends and colleagues.

Caden Marsh
Cyber Security Expert

Last week I attended Ethical hacking and network defence training. My experience with virtual training was very good as I was getting trained in my pleasant environment. My trainer Lee was very experienced and helped me with my doubts with his topic examples. The content was excellent, easy to understand and met all my expectations. Definitely do another course from here.

Shay Jones
Ethical Hacking Trainer

Last week I attended ethical hacking and penetration testing training from the knowledge academy. My tutor for this training course was Alex, and he was really accommodating. The study material was designed in a precise way. I want to thank the trainer for being so patient and polite to answer all the queries coherently. I would recommend this training course to everyone who wants to get a good understanding of hacking.

Skye Gordon
Information Security Consultant

I have completed my Ethical Hacking Professional training and had a great learning experience. I liked the content, and also my trainer Jordan. He was such a superb person, and he skilfully taught each topic. He helped me whenever I had any doubts and gave answers to most of my queries. It was helpful for me to enhance my skills to achieve a key milestone in my career.

Quinn Smith
Associate Growth Hacker

I took the Ethical Hacking and Penetration Testing Training course and found it excellent and convenient. Choosing the knowledge academy website was great in quality and provided me with the best value for my money. The study material was made perfectly precise and contained all the important information. I felt glad to choose this course from here and will recommend this course to everyone.

Nicky Willis
Cybersecurity Engineer
Frequently Asked Questions
What is Ethical Hacking?

Ethical Hacking is the procedure of identifying vulnerabilities in an application, system, or association's infrastructure that an attacker can exploit.
What are the benefits of Ethical Hacking?

It helps in fighting against national security breaches and cyber terrorism, building a system that prevents penetration by hackers, protecting financial and security establishments, etc.
I am unable to find the course that I am looking for.

The Knowledge Academy provides training on over 3000 different subjects. Please contact us if you are unable to find your ideal course in the above course list.
What will I learn during the Ethical Hacking Training?

During the Ethical Hacking training, you will learn various essential topics such as concepts of SQL injection, skill of wireless attacks, buffer overflow, etc. You will also learn about ethical hacking methodologies, network security, malware and malware analysis, and many more concepts.
Will this training help me to get a better job with a high salary package?

Individuals who hold the skills required for conducting Ethical Hacking get higher ranks in companies and get paid more than an average IT Professional.
What are the different skill of wireless and mobile device attacks?

SMiShing, war driving, WPA attack, Bluejacking, replay attacks, bluesnarfing, and RF jamming are the different skill of wireless and mobile device attacks.
Can you customise training material according to our company requirements?

Yes, we have subject matter experts who will work according to your company requirements.
Can The Knowledge Academy deliver corporate/in-house training?

Yes, our specialised in-house/corporate delivery staff constantly works to provide training to our clients who wish to have the convenience and comfort of learning within their familiar surroundings.


 Back
Back
 01344203999
01344203999  Get A Quote
Get A Quote
 Ethical Hacking
Ethical Hacking  40% Off Limited Time Offer
40% Off Limited Time Offer
 Request More Information
Request More Information
 Find Out More
Find Out More
 Want to Know More?
Want to Know More?

