We may not have the course you’re looking for. If you enquire or give us a call on +44 1344 203999 and speak to our training experts, we may still be able to help with your training requirements.
Training Outcomes Within Your Budget!
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

Are you an Ethical Hacker or Web Tester aiming to optimise your workflow and searching for the ideal toolkit? If you're new to the field or looking to enhance your testing practices, leveraging Kali Linux Tools can significantly simplify your testing paradigm. With the wide variety of tools, both commercial and open-source, available within Kali Linux, the challenge lies in selecting the most effective ones for your needs.
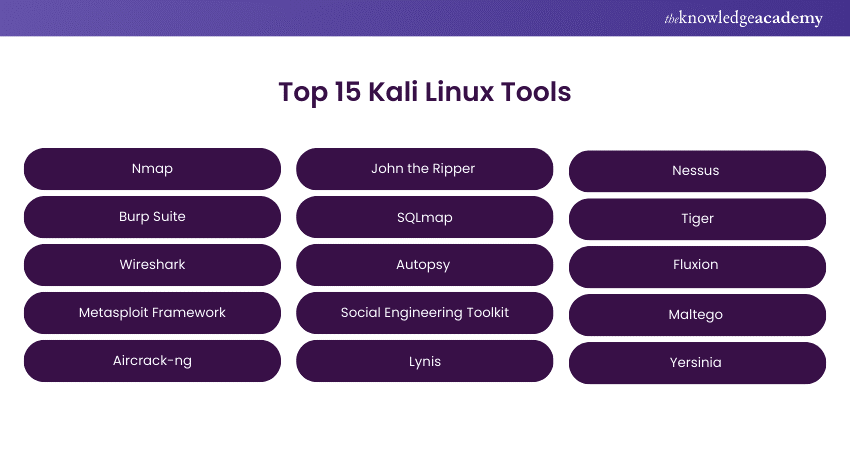
This comprehensive blog addresses your concerns by presenting a curated list of the top 15 Kali Linux Tools, streamlining your Cybersecurity endeavours. Whether you're a seasoned professional or just starting, this blog will assist you in navigating the vast array of tools, ensuring you choose the right ones to boost your efficiency and effectiveness in Ethical Hacking and Web Testing.
Table of Contents
1) What is Kali Linux?
2) Top 15 Kali Linux Tools
a) Nmap
b) Burp Suite
c) Wireshark
d) Metasploit Framework
e) aircrack-ng
f) John the Ripper
g) SQLmap
h) Autopsy
3) Conclusion
What is Kali Linux?
Kali Linux is a powerful open-source Operating System designed for Penetration Testing, Ethical Hacking, and Cybersecurity tasks. Developed by Offensive Security, it provides a comprehensive platform with a vast array of pre-installed security tools and utilities. Kali Linux is based on Debian and incorporates a streamlined and efficient environment for security professionals and enthusiasts.
Its extensive toolset encompasses vulnerability analysis, digital forensics, and network analysis, making it a go-to for security experts. Kali Linux is regularly updated to stay at the forefront of security testing methodologies. Widely used in both professional and educational settings, Kali Linux empowers users to assess and fortify the security of systems, networks, and applications, contributing significantly to Cybersecurity.
Top 15 Kali Linux Tools
This section of the blog will shed light on some of the crucial Kali Linux Tools that can help you with your Cybersecurity initiatives:
1) Nmap
Nmap, short for Network Mapper, is a versatile and indispensable tool in network exploration and security auditing. Recognised for its adaptability, it excels in discovering hosts, services, and potential vulnerabilities within computer networks.
Nmap's prowess lies in its ability to meticulously explore network environments, providing a comprehensive overview of the connected hosts and their services. Its versatility extends to identifying potential security loopholes, making it an essential asset for security professionals and network administrators.
Functionality:
The functionality of Nmap spans a spectrum of crucial tasks within network security. It begins with host discovery, efficiently locating active devices within the network. Moving beyond, it excels at service version detection, providing insights into the types of services running on discovered hosts. Nmap's multifaceted capabilities extend to vulnerability identification, allowing security practitioners to assess weaknesses and fortify the network against threats.
2) Burp Suite
Burp Suite stands out as an indispensable Web Application Testing tool renowned for identifying security vulnerabilities in web applications. Developed to enhance Cybersecurity, Burp Suite offers a robust set of features for comprehensive testing. Its capabilities extend beyond automated scanning to include manual testing tools, making it a preferred choice for security professionals and ethical hackers.
Functionality:
Proxy, Spider, Scanner, and Intruder modules enrich Burp Suite's functionality. The Proxy module facilitates intercepting and inspecting traffic between the user and web applications. The Spider module automates the crawling process, mapping out application content and structure. The Scanner module, a highlight of Burp Suite, employs advanced algorithms to identify vulnerabilities systematically. Lastly, the Intruder module enables users to customise and automate attacks, uncovering potential security issues that demand attention.
3) Wireshark
Wireshark is a widely recognised network protocol analyser, holding paramount importance in Cybersecurity. Its primary function revolves around enabling users to capture and analyse data in real-time within a network. Developed as an open-source tool, Wireshark has become an invaluable asset for professionals and enthusiasts, facilitating a deeper understanding of network traffic patterns and aiding in troubleshooting.
Functionality:
Wireshark's functionality is characterised by its ability to provide a granular view of network packets. This nuanced perspective allows users to delve into the intricate details of data transmission, facilitating the identification of anomalies and potential security threats. By capturing and dissecting packets, Wireshark empowers users to scrutinise the flow of information, detect irregularities, and pinpoint the root causes of network issues. Its real-time analysis capabilities contribute to effective network management, ensuring optimal performance and heightened security measures.
4) Metasploit Framework
The Metasploit Framework stands as a pinnacle in Cybersecurity, recognised for its prowess in Penetration Testing. An open-source platform, it serves as a robust foundation for the development, testing, and execution of exploit code. Metasploit, developed by Rapid7, has evolved into a comprehensive toolkit trusted by security professionals worldwide.
Functionality:
Security experts utilise the power of Metasploit to navigate the complex landscape of Cybersecurity challenges. Its functionality extends beyond mere exploitation, encompassing various activities crucial in fortifying digital defences. Professionals utilise Metasploit to pinpoint vulnerabilities, execute precise exploits, and delve into post-exploitation manoeuvres. The framework's versatility enhances the efficacy of Penetration Testing, providing a dynamic and adaptive approach to securing systems and networks.
5) Aircrack-ng
Aircrack-ng is a comprehensive suite of network software tools meticulously crafted to evaluate Wi-Fi network security. This multifaceted suite encompasses a range of utilities, notably excelling in packet capturing and password cracking. Tailored for professionals in the field, Aircrack-ng facilitates an in-depth assessment of Wi-Fi network vulnerabilities, enabling users to identify potential security loopholes and implement robust countermeasures.
Functionality:
The suite's packet-capturing capabilities empower security experts to scrutinise network traffic, analysing data packets for potential weaknesses. Aircrack-ng's password-cracking functionalities prove invaluable for testing the strength of WEP and WPA/WPA2-PSK encryption protocols, aiding in the identification of weak passwords and potential points of unauthorised access. Aircrack-ng is a powerful ally in the quest for heightened Wi-Fi security, offering professionals the tools needed to bolster defences and ensure the integrity of wireless networks.
Unlock your testing expertise with our Kali Linux Fundamentals Course – Sign up today!
6) John the Ripper
John the Ripper is a renowned password-cracking tool widely acknowledged for its efficiency in uncovering weak passwords across diverse security settings. This versatile software employs various attack methods, making it a crucial asset for evaluating password strength and bolstering overall security measures. Whether executing brute-force attacks or dictionary-based approaches, John the Ripper excels in systematically analysing password vulnerabilities.
Functionality:
In brute-force attacks, the tool systematically attempts every possible combination until the correct password is identified, allowing for a comprehensive assessment of a system's susceptibility to such methods. Alternatively, John the Ripper leverages pre-compiled lists of commonly used passwords and phrases through dictionary attacks, streamlining the process of identifying weak or easily guessable passwords.
7) SQLmap
SQLmap is a pivotal tool in Cybersecurity, offering automated capabilities for identifying and exploiting SQL injection vulnerabilities, a prevalent and potentially damaging issue in web application security. This tool is mainly instrumental for security professionals, Penetration Testers, and ethical hackers who seek to assess and fortify the resilience of web applications against SQL injection attacks.
Functionality:
The functionality of SQLmap is underscored by its intuitive Command Line Interface (CLI), providing users with a powerful yet user-friendly environment for conducting comprehensive security assessments. By automating the detection and exploitation of SQL injection flaws, SQLmap streamlines the complex process of identifying potential weaknesses in database-driven web applications. Its systematic approach involves probing for vulnerabilities, allowing users to uncover possible entry points for attackers attempting to manipulate or compromise databases.
8) Autopsy
Autopsy is a robust digital forensics platform designed to meticulously analyse hard drives and smartphones, providing investigators with powerful tools to unearth crucial digital evidence during forensic examinations. Catering to the growing demand for thorough investigations in the digital age, Autopsy is a go-to solution for professionals in the field.
Functionality:
Its multilayered functionality includes comprehensive file system analysis, enabling investigators to scrutinise storage structures for hidden or deleted data. Autopsy's keyword searching capabilities further enhance its utility, allowing for identifying relevant information amid vast datasets. The platform's timeline analysis feature aids in reconstructing digital activities chronologically, providing investigators with a cohesive narrative of events. Autopsy's user-friendly interface and automation features contribute to the efficiency of digital forensics tasks, facilitating a streamlined investigative process.
9) Social Engineering Toolkit
The Social Engineering Toolkit (SET) is a potent compilation of tools and utilities specifically crafted for simulating a diverse range of social engineering attacks. Aimed at security professionals, SET is crucial in fortifying organisational defences against prevalent social engineering threats such as phishing and credential harvesting.
Functionality:
SET's functionality empowers security experts to conduct realistic and controlled simulations to identify potential vulnerabilities in an organisation's human factor. By simulating phishing attacks and other forms of social engineering, SET facilitates a hands-on assessment of how well employees can resist or fall victim to manipulation, thus aiding in developing targeted awareness and training programs.
10) Lynis
Lynis is an essential security auditing tool meticulously engineered to evaluate the security posture of Linux and Unix systems. Tailored for System Administrators and security professionals, Lynis conducts comprehensive scans to identify vulnerabilities, assess system configurations, and deliver insightful recommendations for enhancing security.
Functionality:
The functionality of Lynis spans a wide array of security assessments, including thorough examinations of system configurations. By checking for adherence to security best practices, the tool provides a robust mechanism for users to ensure their systems are configured in line with industry standards. Lynis goes beyond mere vulnerability identification; it offers actionable insights into potential security gaps, equipping users with the information needed to implement effective system-hardening measures.
11) Nessus
Nessus is a versatile and comprehensive vulnerability scanner, which is crucial in identifying security vulnerabilities within networks, systems, and applications. Designed to meet the needs of Cybersecurity professionals and organisations, Nessus plays a pivotal role in proactive vulnerability management, contributing to maintaining a robust security posture.
Functionality:
The functionality of Nessus is characterised by its expansive database, housing a wealth of information on known vulnerabilities. Leveraging this extensive repository, the tool conducts systematic scans, thoroughly examining target environments to pinpoint potential weaknesses. By providing detailed reports on identified vulnerabilities, Nessus empowers security teams to take preemptive action, addressing potential threats before malicious actors can exploit them.
Learn more about testing with our Tools and Techniques for Penetrating Testing Course – Join today!
12) Tiger
The Tiger Security Tools Collection is a specialised suite designed to address Unix-like systems' security auditing and intrusion detection requirements. Tailored for Unix-based environments, Tiger serves as a valuable resource for enhancing the overall security posture of these systems.
Functionality:
The functionality of Tiger revolves around its ability to conduct systematic system checks. Tiger identifies and flags security vulnerabilities, misconfigurations, and potential risks within the Unix-like environment through these assessments. This proactive approach to security auditing is crucial for preemptively addressing weaknesses that malicious actors could exploit. By offering insights into security gaps and potential threats, Tiger plays a pivotal role in fortifying the security hygiene of Unix-based systems.
13) Fluxion
Fluxion is a specialised Wi-Fi analysis tool uniquely designed for executing social engineering attacks, focusing on rogue Wi-Fi access points and credential harvesting. Tailored for security professionals and ethical hackers, Fluxion automates the intricate process of setting up deceptive Wi-Fi networks, enticing target devices, and capturing login credentials. Its functionality provides a hands-on illustration of potential weaknesses in Wi-Fi security.
Functionality:
The tool's primary function involves the automated creation of rogue Wi-Fi access points that mimic legitimate networks. As unsuspecting devices connect to these deceptive networks, Fluxion initiates a series of simulated attacks to capture login credentials, showcasing users' susceptibility to such social engineering tactics. This automated approach streamlines the execution of complex attacks, making Fluxion an efficient tool for testing and raising awareness about the risks associated with insecure Wi-Fi connections.
14) Maltego
Maltego is a powerful and versatile data visualisation tool for link analysis and Open-Source Intelligence (OSINT) investigations. Its functionality revolves around mapping and connecting diverse data points across the internet to generate visual representations of relationships and patterns. Maltego excels in aggregating information from various sources, such as social media platforms, domain registries, and public databases.
Functionality:
Its intuitive interface enables users to explore, analyse, and visualise complex information networks. Maltego facilitates identifying connections between individuals, organisations, and digital assets, making it a valuable tool for Cybersecurity professionals, investigators, and intelligence analysts. Its capabilities extend to uncovering potential threats, investigating cyber incidents, and aiding in proactively identifying vulnerabilities. Maltego's adaptability and extensive data integration contribute to its reputation as an indispensable tool for conducting comprehensive and visually insightful investigations in Cybersecurity and intelligence.
15) Yersinia
Yersinia is a specialised network tool crafted to exploit various network protocols, particularly in testing and enhancing network security. Geared towards security professionals and ethical hackers, Yersinia is instrumental in identifying and addressing vulnerabilities within network infrastructures through its targeted focus on protocol-based attacks.
Functionality:
The functionality of Yersinia revolves around its capacity to simulate and exploit weaknesses in network protocols, allowing security experts to assess the robustness of their network defences. By executing protocol-based attacks, Yersinia assists in identifying potential entry points and weaknesses that malicious actors could exploit. This tool empowers security professionals to proactively test and fortify network security measures, ultimately contributing to developing more resilient and secure network infrastructures in the face of evolving cyber threats.
Master the testing expertise with our Fundamentals of Test Automation Course – Sign up today!
Conclusion
In conclusion, this curated list of the 15 Best Kali Linux Tools provides a valuable resource for Ethical Hackers and Web Testers. By strategically incorporating these tools into your workflow, you can optimize your Cybersecurity efforts and navigate the vast array of Kali Linux Tools with confidence, ensuring enhanced efficiency and effectiveness
Learn more about testing with our Unit Testing Course – Join today!
Frequently Asked Questions

Essential for beginners, tools like Wireshark, Nmap, and Burp Suite offer foundational capabilities in network analysis, scanning, and Web Application Testing, guiding newcomers in ethical hacking and web testing within Kali Linux.

Yes, these Kali Linux Tools serve dual purposes. Metasploit, Aircrack-ng, and Nikto, among others, are versatile, aiding both penetration testing by identifying vulnerabilities and performing comprehensive assessments.

Frequent updates are a priority for Kali Linux Tools, ensuring users access cutting-edge features and patches. Utilize the built-in package management tools like apt to effortlessly update tools, maintaining optimal performance and security.

The Knowledge Academy takes global learning to new heights, offering over 30,000 online courses across 490+ locations in 220 countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 17 major categories, we go the extra mile by providing a plethora of free educational Online Resources like News updates, Blogs, videos, webinars, and Interview Questions. Tailoring learning experiences further, professionals can maximise value with customisable Course Bundles of TKA.

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.

The Knowledge Academy offers various Automation Courses including Kali Linux, Fundamentals of Test Automation, etc. These courses cater to different skill levels, providing comprehensive insights into Kali Linux skills.
Our IT Security and Data Protection blogs covers a range of topics related to testing skills, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your Testing skills, The Knowledge Academy's diverse courses and informative blogs have you covered.
Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 Tools and Techniques for Penetrating Testing
Tools and Techniques for Penetrating Testing
Thu 23rd Jan 2025
Thu 27th Mar 2025
Thu 15th May 2025
Thu 17th Jul 2025
Thu 25th Sep 2025
Thu 13th Nov 2025







 Top Rated Course
Top Rated Course



 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


