We may not have the course you’re looking for. If you enquire or give us a call on +44 1344 203999 and speak to our training experts, we may still be able to help with your training requirements.
Training Outcomes Within Your Budget!
We ensure quality, budget-alignment, and timely delivery by our expert instructors.

The Certified Information System Security Professional (CISSP) certification is the gold standard for information security certifications. It is awarded by the International Information System Security Certification Consortium (ISC)², a non-profit organisation specialising in training and certifying cybersecurity professionals. These certifications are geared towards experienced professionals. Given how difficult the exam is, (ISC)² encourages the candidates to undertake CISSP Practice Exams.
According to Statista, CISSP is the most popular cybersecurity certification held by 38% of professionals globally. Getting CISSP certification is no easy task, but fortunately, (ISC)² provides many resources like the CISSP All-in-One Exam Guide and the official Common Book of Knowledge (CBK). Using these resources with easily available online CISSP Practice Exam questions can make the exam easier. Check out these CISSP Practice Exam questions and answers to prepare for your certification exam. Start preparing now to crack your exam!
Table of Contents
1) CISSP Practice Exam Questions and Answers
a) Which factors are the most important to make sure that the organisation is secure?
b) When using open-source applications, what is the biggest security risk for the organisation?
c) If designed securely, what do the retinal and fingerprint scanners do when enrolling a new user?
d) Which of the following is Layer 3 device?
2) Conclusion
CISSP Practice Exam Questions and Answers
CISSP is not easy and has a relatively low pass rate compared to other certifications. Practising with CISSP Practice Exam questions can significantly improve your chance of passing and earning the certificate. The exam will contain questions from eight domains (or topics) with respective weightage:
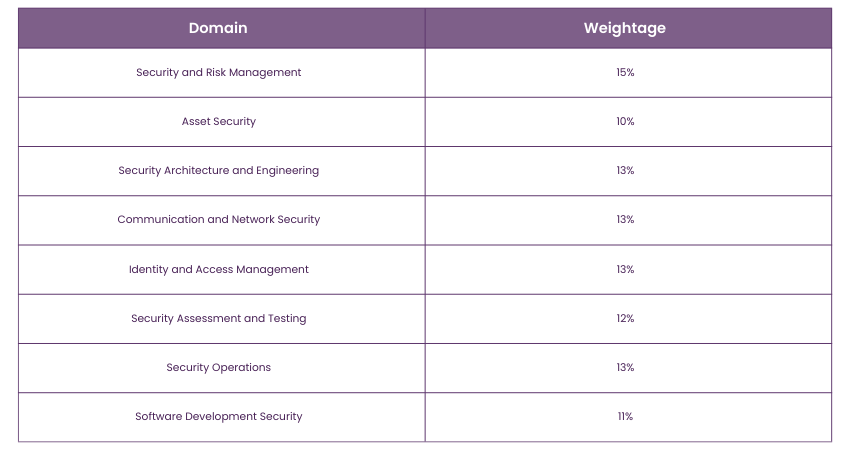 Source: (ISC)²
Source: (ISC)²
The following questions showcase the questions that usually appear in the examination.
1) Which factors are the most important to make sure that the organisation is secure?
a) The support of the senior management
b) Efficient implementation methods and control
c) Awareness of security
d) Up-to-date security policies and procedures
Answer: a) It is not possible to have a good security in place for the organisation if there is no proper support from the senior management
2) For a large enterprise that wants to ensure that security operations are following industry standards, what is the best solution to d(ISC)²ourage malicious activities? What type of control framework should be focused on?
a) Preventative controls
b) Assessment controls
c) Detective controls
d) Deterrent controls
Answer: d) Deterrent controls are the most appropriate for blocking malicious activities. For example, the implementation of a firewall.
3) Let’s say an employee has received an email and he believes that it was sent by a colleague. However, the email was spoofed and sent by an attacker. What security measures would have indicated this spoofed email attack?
a) Integrity
b) Authorisation
c) Non-repudiation
d) Privacy
Answer: c) Non-repudiation is a combination of integrity and authenticity. This is implemented using digital signatures.
Learn how to protect your organisation from cybersecurity threats and improve information security with the CISSP Training.
4) When using open-source applications, what is the biggest security risk for the organisation?
a) The developer of the application might not have used secure development practices.
b) Source code is visible to anyone worldwide, which might put the application at risk.
c) The developers might not continue its further development, provide updates and security patches
d) The operation team at the organisation might not be prompt at updating the application with the latest patches and updates.
Answer: a) The organisation cannot determine if the developer or the creators have used secure practices for the development.
5) What is the best way to send a message securely to someone who is several network hops away from the person sending the message?
a) Secure Multipurpose Internet Mail Extensions (S/MIME)
b) Point-to-Point Tunnelling Protocol (PPTP)
c) Link encryption
d) Secure Shell (SSH)
Answer: a) S/MIME is used for encrypting and digital signing a message or an email for secure transmission using public key infrastructure (PKI).
6) What method will you recommend out of the following to maximise the protection of your organisational data and to minimise the data remanence.
a) Data encryption
b) Physical destruction
c) Formatting values
d) Data classification
Answer: b) Physical destruction is one of the three established methods used for data protection. The other two methods are degaussing and overwriting of data.
7) Which of the following is the most probable cause if a Layer 1 network issue has caused a communication problem?
a) Network Interface Card (NIC)
b) Switch
c) Cable
d) Router
Answer: c) Layer 1 in the OSI Reference Model is also called the “Physical Layer” as it provides a physical connection to the network. Any device that provides a physical path for the network to traverse is a Layer 1 device. For example, cables, connectors, hubs, etc
8) If designed securely, what do the retinal and fingerprint scanners do when enrolling a new user?
a) Convert the image of the retinal and fingerprint scan into a hash
b) Save the image of the retinal and fingerprint scan and then encrypt the image
c) Save the image of the retinal and fingerprint scan
d) Convert the image of the retinal and fingerprint scan into a hash and then encrypt the hash
Answer: d) Hashing is a more secure way of storing information than encryption. If the system is designed securely, the stored retinal and fingerprint data will be converted into a hash and then encrypted.
9) The alignment of security controls with the business objectives is a fundamental principle. Why is this concept important based on the impact security has on the organisation’s success?
a) Implementing security measures is too expensive for smaller organisations
b) There is always a trade-off between the cost and benefits of the security measures
c) Security measures are very important and must be implemented everywhere
c) It is better to ensure security than to face potential losses.
Answer: b) In some situations, security measures can negatively affect performance, ease of use and backward compatibility. An organisation must look at the overall business objectives and its primary needs to set security measures. A small organisation does not need military-grade security.
10) Which of the following is Layer 3 device?
a) LAN cable
b) Router
c) Switch
d) NIC
Answer: b) The Router is a Level 3 device which is the Network layer.
Gain an understanding of virtual private networks with our Information Systems Security Management Course- sign up now!
11) Which of the following best describes the mitigation of data remanence by an overwriting process?
a) Converting data into encrypted format
b) Reducing magnetic field patterns on storage media
c) Exposing storage media to corrosive chemicals
d) Replacing existing data with new patterns of 1's and 0's
Answer: d) Data remanence can be addressed by completely rewriting every bit on the storage medium. This can be achieved by filling the storage with all 0's, all 1's, a consistent pattern, or a random sequence. Enhanced effectiveness can be achieved by repeating this procedure multiple times using various patterns.
12) What is an advantage of RSA over DSA?
a) Greater resistance to quantum computing attacks
b) Smaller key sizes for equivalent security
c) Faster key generation
d) Better performance in digital signatures
Answer: a) Greater resistance to quantum computing attacks. RSA serves for data encryption, key exchange, and digital signatures, whereas DSA is solely applicable for digital signatures.
13) Which of the following statements best describes the purpose of polyinstantiation?
a) To enhance data security by encrypting sensitive information
b) To prevent data loss through regular backups
c) To ensure different security levels for the same data in a multilevel security system(MLS)
d) To improve data accessibility for authorised users
Answer: c) To ensure different security levels for the same data in a multilevel security system(MLS). Instantiation refers to the creation of an object from a class. In contrast, polyinstantiation involves creating multiple objects and modifying one of the copies to have distinct attributes. There are several motives for employing polyinstantiation. An illustrative use case discussed in the chapter pertains to enhancing security. It serves as a means to prevent a lower-level subject from accessing an object at a higher level.
14) Which of the following best defines Synthetic Transactions?
a) Simulating network activity with artificial data
b) Recording and playing back real user interactions
c) Automating repetitive tasks in software development
d) Analysing system logs for security threats
Answer: a) Simulating network activity with artificial data. Synthetic transactions are designed to replicate the actions of genuine users, yet they do not stem from actual user interactions with the system. These transactions provide organisations with a means to verify the proper functionality of their services, eliminating the need to depend solely on user grievances to identify issues.
15) Why might an organisation need to periodically test effective and proven disaster recovery and business continuity plans?
a) To ensure compliance with industry regulations.
b) To identify weaknesses and areas for improvement.
c) To reduce the overall cost of data recovery.
d) To demonstrate preparedness to stakeholders and investors.
Answer: b) To identify weaknesses and areas for improvement. Regular testing of DRPs and BCPs is vital to gauge their adaptability in the face of environmental changes, be it internal or external. As the business landscape is dynamic, modifications to these plans are inevitable. Neglecting periodic testing poses the risk of prolonged system downtimes, underscoring the importance of ensuring these plans remain resilient, adaptable, and capable of mitigating unexpected disruptions.
16) Which of the following features enables code to be executed without the usual security checks?
a) Maintenance hooks
b) NoSQL database
c) Cross-Site Scripting (XSS)
d) Unsafe reflection
Answer: a) Maintenance hooks. Maintenance hooks bypass the security and access control measures of a system or application, granting access to those familiar with the key sequence. Removing maintenance hooks from the code before deploying it in a production environment is essential to maintain security and prevent unauthorised access to the application and its underlying code.
17) What is the Kerberos authentication method?
a) A public key encryption method
b) A symmetric key encryption method
c) An authentication protocol for secure networks
d) An open-source password hashing method
Answer: c) An authentication protocol for secure networks. Kerberos is an authentication method designed to verify the identities of users or entities in a networked environment. It relies on secret key cryptography to securely authenticate users, enabling them to access network resources without revealing their passwords.
Conclusion
These CISSP Practice Exam questions can give you a rough idea of the type of questions that appear on the exam. They are asked at the conceptual level, so there might be a better practical answer among the given options. Start preparing now to crack your CISSP Exam!
Learn about the eight core domains of IT Security with our CISSP Certification Course - sign up now!
Frequently Asked Questions

It is considerably challenging. However, with proper preparation and resources, this exam is passable. It is designed to ensure that the people who crack it are well-suited for this industry.

The CISSP pass rate is approximately 20%.

The Knowledge Academy takes global learning to new heights, offering over 30,000 online courses across 490+ locations in 220 countries. This expansive reach ensures accessibility and convenience for learners worldwide.
Alongside our diverse Online Course Catalogue, encompassing 17 major categories, we go the extra mile by providing a plethora of free educational Online Resources like News updates, Blogs, videos, webinars, and interview questions. Tailoring learning experiences further, professionals can maximise value with customisable Course Bundles of TKA.

The Knowledge Academy’s Knowledge Pass, a prepaid voucher, adds another layer of flexibility, allowing course bookings over a 12-month period. Join us on a journey where education knows no bounds.

The Knowledge Academy offers various CISSP Courses, including Certified Information Systems Security Professional Course, CISSP-ISSAP Course and Information Systems Security Management Course. These courses cater to different skill levels, providing comprehensive insights into What is Information Governance.
Our IT Security & Data Protection Blogs cover a range of topics related to Scrum, offering valuable resources, best practices, and industry insights. Whether you are a beginner or looking to advance your Business Improvement skills, The Knowledge Academy's diverse courses and informative blogs have you covered.
Upcoming IT Security & Data Protection Resources Batches & Dates
Date
 CISSP Certification
CISSP Certification
Mon 6th Jan 2025
Mon 24th Mar 2025
Mon 19th May 2025
Mon 14th Jul 2025
Mon 8th Sep 2025
Mon 17th Nov 2025







 Top Rated Course
Top Rated Course



 If you wish to make any changes to your course, please
If you wish to make any changes to your course, please


